How Face Recognition Technology Works: Security and Biometric Identity
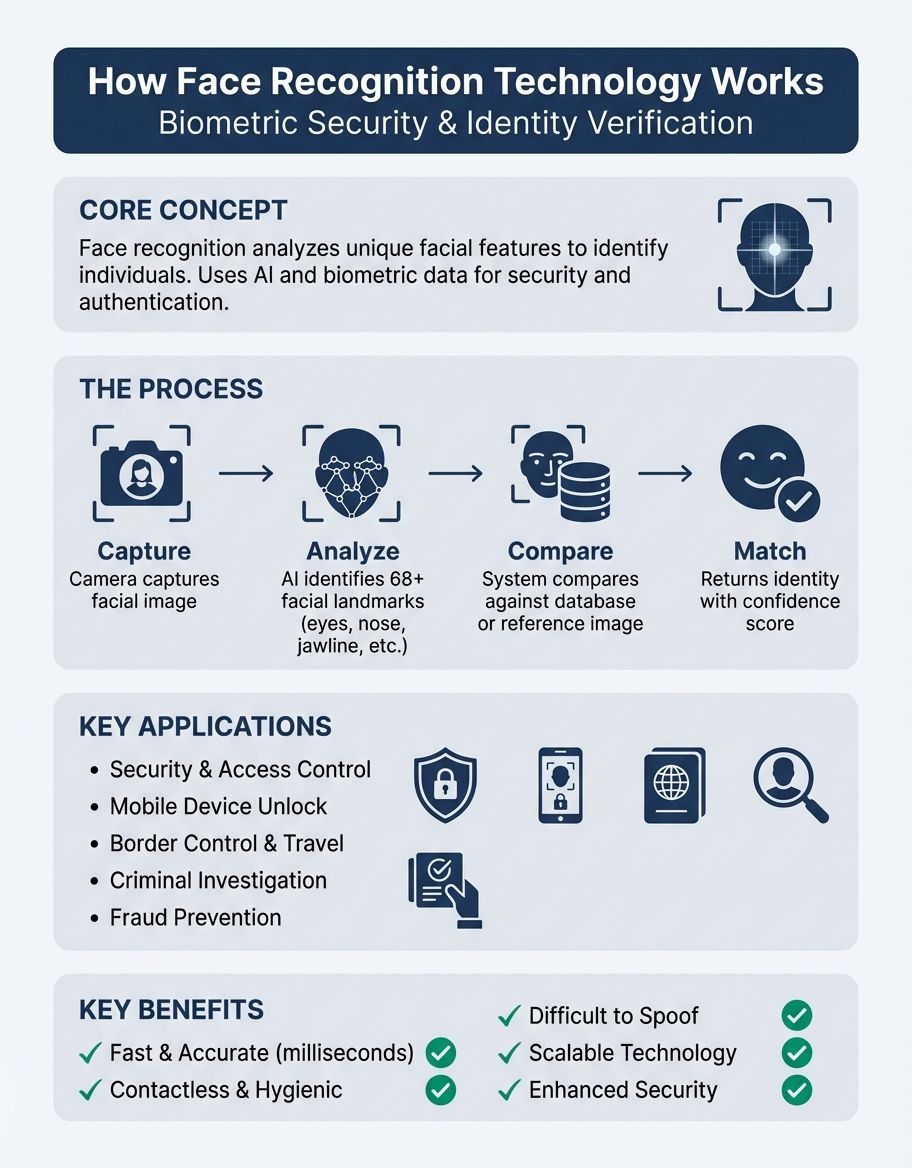
Understanding how face recognition technology works reveals one of the most transformative innovations in security and authentication. This facial recognition technology analyzes unique features of a person's face to identify individuals across countless applications. From unlocking smartphones to enhancing security systems, this innovation has become integral to modern digital infrastructure. Sophisticated methods enable systems to capture, analyze, and match facial patterns with remarkable accuracy, making facial recognition a cornerstone of contemporary authentication.
Understanding Facial Recognition Technology Fundamentals
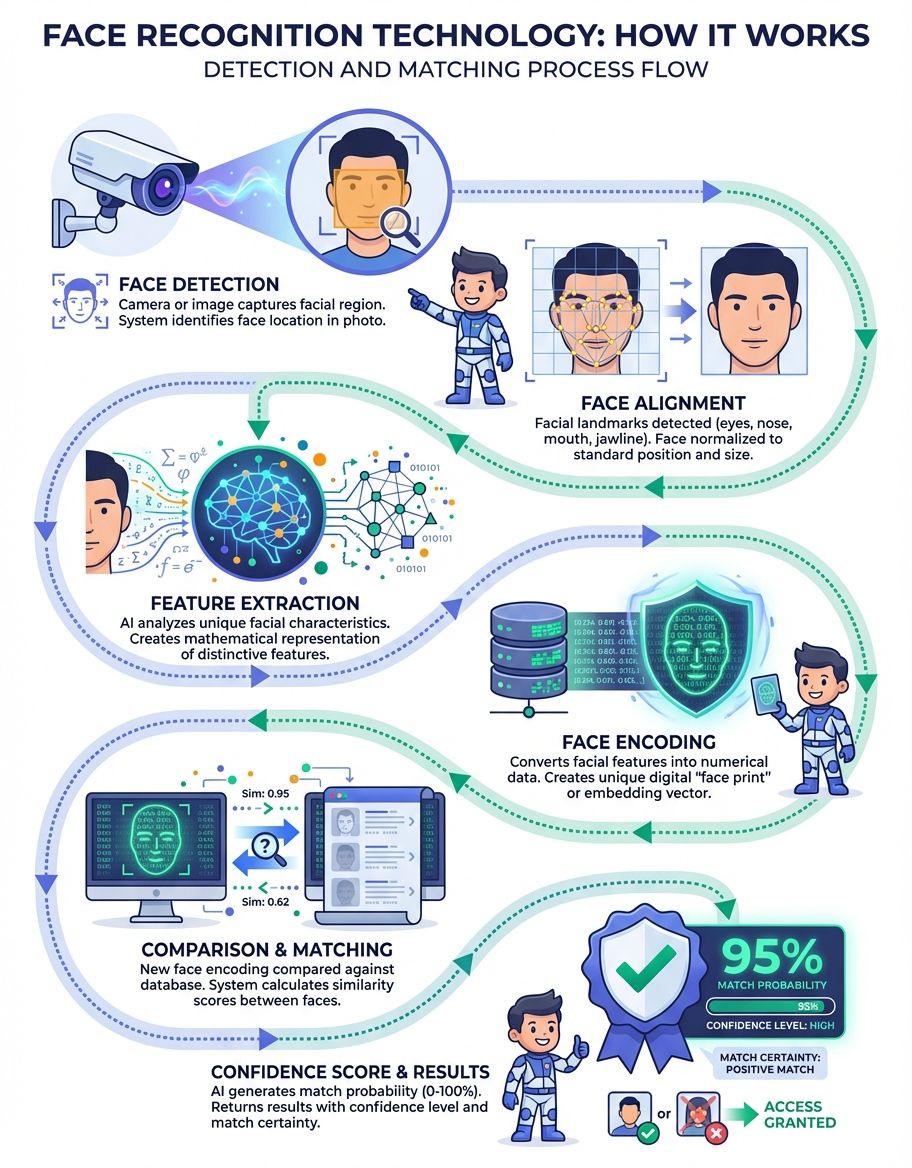
Facial recognition technology operates through a sophisticated process that begins with capturing a digital image or video frame of a person's face. The system uses optical input devices such as cameras to detect faces in video streams or still images. Once the image is captured, specialized software analyzes the unique geometry of each person's face, measuring biometric features including the distance between eyes, nose width, jawline structure, and other distinctive characteristics that define each individual's identity.
The technology identifies individuals by mapping these facial features and converting them into numerical data points called a facial signature. This template represents the unique aspects of the human face. Modern face recognition systems employ advanced methods that can process this data rapidly, even when analyzing faces from different angles or under varying lighting conditions. The matching process compares this newly created template against existing templates stored in a database to determine if there's a similarity match.
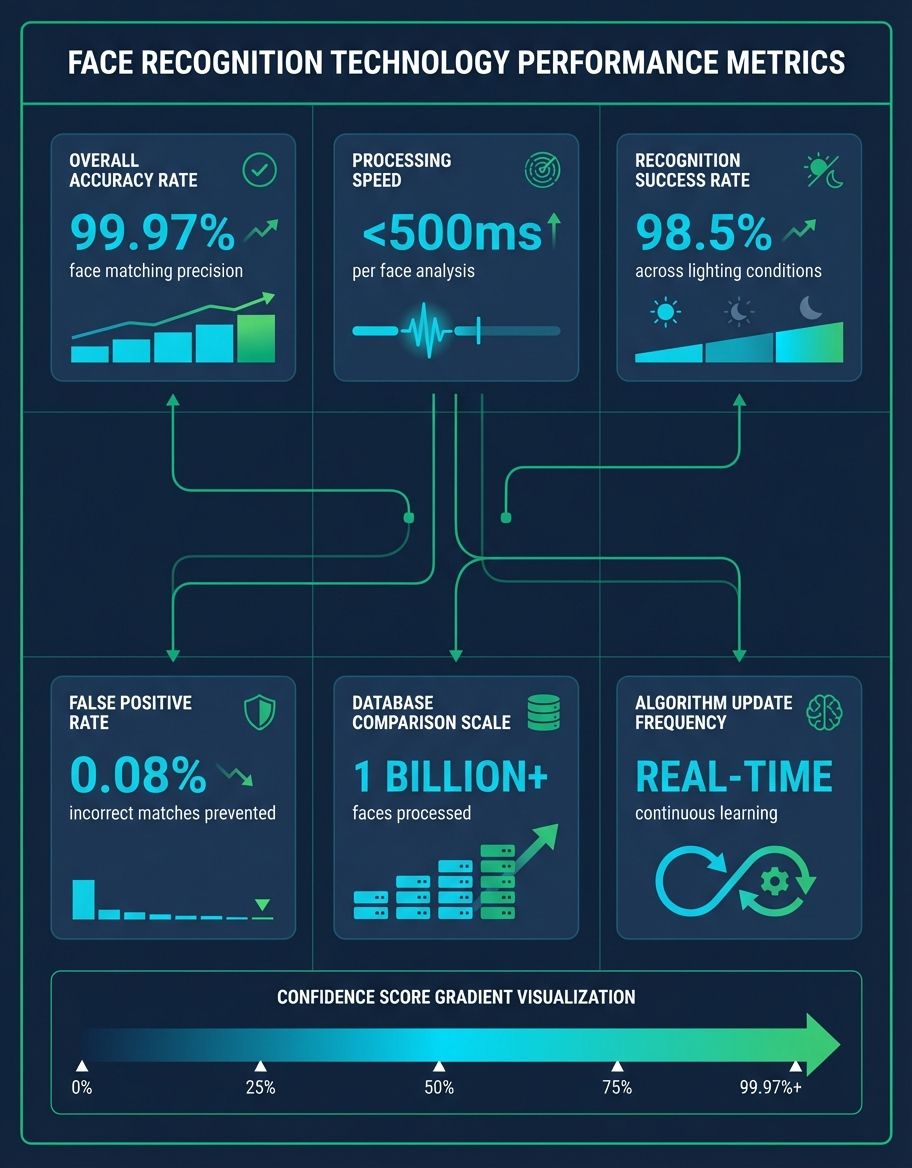
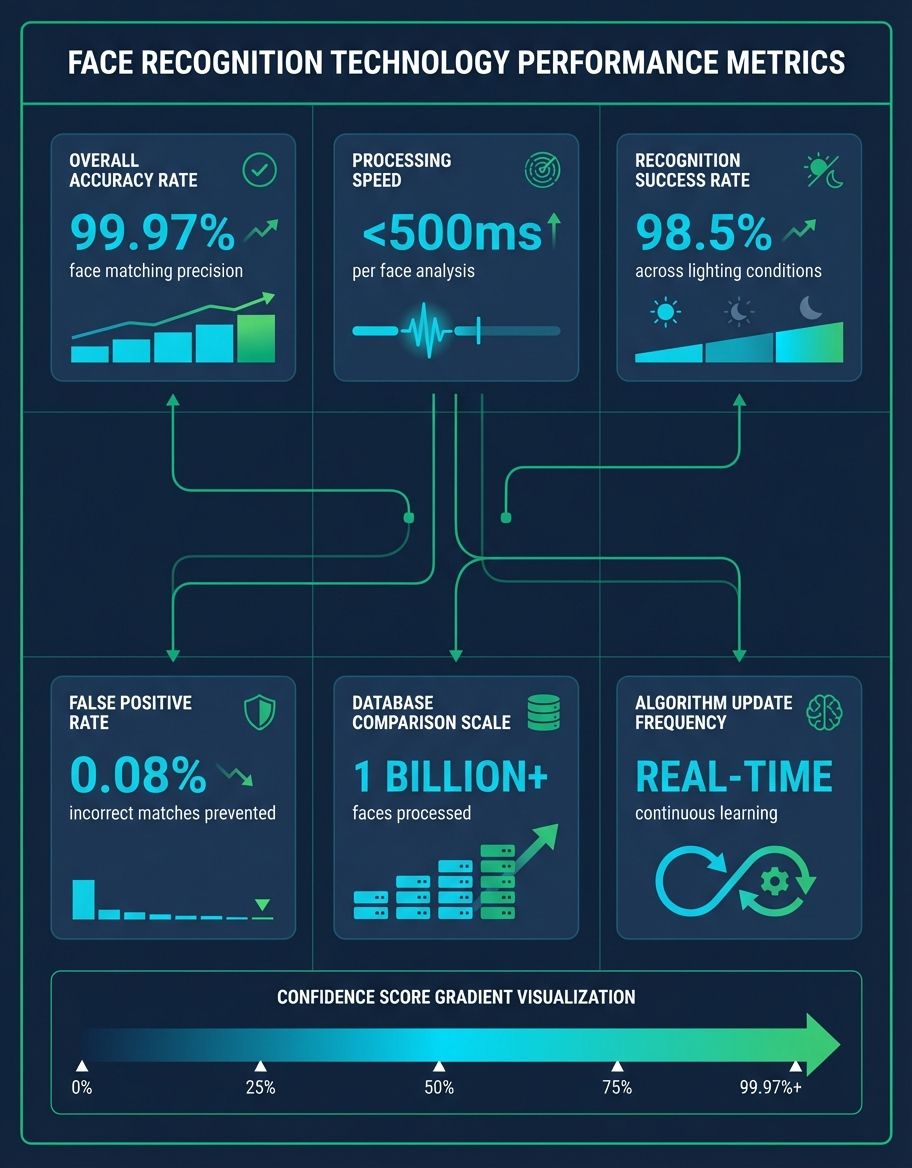
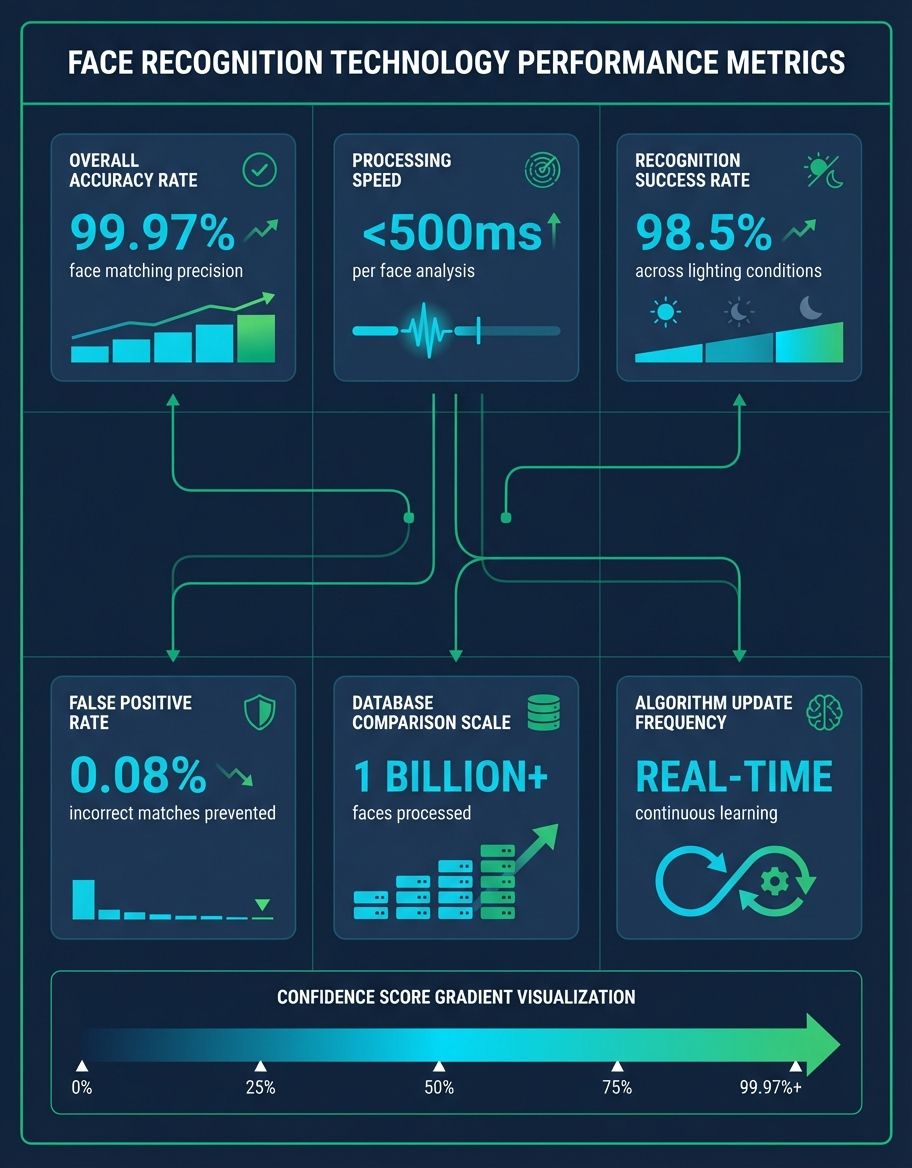
Face recognition has evolved significantly, with current systems capable of detecting faces in video with impressive speed and accuracy. The software analyzes each frame, identifying facial landmarks and creating a comprehensive map of the person's facial structure. This process happens in milliseconds, enabling real-time authentication across numerous applications from security checkpoints to social media platforms.
Storage Systems and Database Management in Facial Recognition
Storage infrastructure forms the backbone of effective facial recognition deployment. These systems require robust storage solutions to maintain vast databases of facial templates, often containing millions of individual records. Enterprise-level storage systems must handle both the initial facial data captured during enrollment and the ongoing storage of verification attempts and system logs.
Azure and other platforms have emerged as popular solutions for facial recognition databases, offering scalability and accessibility advantages. Organizations can leverage these infrastructures to store facial templates securely while ensuring rapid retrieval during matching processes. However, storage security remains paramount, as facial data represents sensitive personal information requiring stringent measures.
The storage architecture must accommodate continuous growth as new individuals are enrolled and existing records are updated. Advanced storage systems implement redundancy protocols to prevent data loss and ensure system reliability. Database optimization techniques help maintain query performance even as storage volumes expand, enabling quick matching operations essential for real-time facial recognition applications.
Modern storage solutions incorporate encryption protocols to protect facial data both at rest and in transit. Organizations implementing facial recognition must balance storage capacity requirements with security considerations, often employing tiered storage strategies that keep frequently accessed templates on high-performance systems while archiving older data. The storage infrastructure directly impacts system performance, with faster storage enabling quicker verification times and improved user experiences.
Security Considerations in Facial Recognition Systems
Security remains a critical concern in facial recognition implementations, encompassing both data safeguarding and process integrity. Robust security measures prevent unauthorized access to facial templates, which could enable theft or misuse if compromised. Organizations deploying facial recognition must implement multi-layered security protocols against both external attacks and internal threats.
Encryption plays a vital role in securing facial recognition systems, with templates encrypted before storage and during transmission between system components. Advanced security architectures employ tokenization techniques, storing only hashed representations of facial signatures rather than the raw biometric data. This approach ensures that even if storage systems are breached, the stolen data cannot easily reconstruct actual facial images.
Access control mechanisms restrict who can view or modify facial recognition databases, with comprehensive audit trails tracking all system interactions. Security protocols must address potential spoofing attacks where malicious actors attempt to fool the system using photographs, videos, or masks. Modern systems incorporate liveness detection features that verify the subject is a living person rather than a static representation.
The security framework extends beyond data safeguarding to include accuracy and preventing false matches. Systems must balance security requirements with usability, implementing sufficient stringency without creating excessive false rejection rates. Regular security audits identify vulnerabilities, while continuous monitoring detects anomalous patterns that might indicate attempted breaches or system compromises.
Privacy, Development, and Surveillance Implications
Privacy concerns represent perhaps the most significant challenge facing facial recognition deployment. The technology's ability to identify individuals without their active participation raises fundamental questions about consent and personal autonomy. Privacy advocates worry about pervasive surveillance enabled by facial recognition, particularly when deployed in public spaces where individuals have limited awareness of monitoring.
Privacy-preserving facial recognition technologies have become a research priority, with techniques like federated learning and differential privacy offering potential solutions. These approaches allow systems to perform matching without centralizing sensitive data, reducing privacy risks. However, balancing functionality with privacy remains an ongoing challenge.
Applications for identifying suspects and locating missing persons have expanded rapidly among law enforcement agencies. While these offer legitimate security benefits, they also enable mass monitoring capabilities that could infringe on civil liberties. Comprehensive governance frameworks help ensure face recognition deployment respects privacy rights while serving legitimate security interests.
Regulatory oversight has accelerated as governments recognize the need for controls on facial recognition technology. Various jurisdictions have implemented restrictions on use in public spaces, while others have banned specific applications altogether. Organizations must navigate this evolving regulatory landscape, ensuring their facial recognition implementations comply with applicable privacy laws and ethical guidelines. Industry standards and best practices help guide responsible deployment that respects individual privacy while enabling beneficial applications.
Microsoft Azure and Cloud-Based Recognition Technology
Microsoft has emerged as a leading provider of cloud-based facial recognition through its Azure platform, offering comprehensive facial recognition capabilities via Azure Cognitive Services. The Azure Face API enables developers to integrate sophisticated facial recognition functionality into applications without building recognition systems from scratch. This cloud approach democratizes access to advanced recognition technology, making it available to organizations of all sizes.
Azure's facial recognition services leverage Microsoft's extensive research in computer vision and machine learning. The platform provides features including face recognition, face detection, matching, and emotion analysis. Organizations can use Azure to build applications ranging from authentication systems to customer experience analytics, all supported by Microsoft's robust infrastructure.
The Azure platform handles the complex storage and computational requirements of this technology, offering scalable solutions that grow with organizational needs. Microsoft implements stringent security protocols protecting facial data stored in Azure, including encryption, access controls, and compliance with various privacy regulations. This technology enables rapid deployment of biometric capabilities without significant upfront infrastructure investments.
Microsoft has also been proactive in addressing ethical concerns around this technology, implementing responsible AI principles and advocating for government regulation. Azure provides tools helping organizations deploy biometric systems responsibly, including capabilities to detect and mitigate bias. This combination of technical capability and ethical consideration makes Azure a popular choice for organizations seeking to implement facial recognition while maintaining privacy and security standards. Azure's comprehensive approach to identity technology balances innovation with responsible deployment practices.
Authentication Processes Using Biometric Technology
This technology operates through distinct modes serving different security requirements. The most common mode confirms that a person matches their claimed identity by comparing a live capture against a stored template. This one-to-one matching process validates claims during login attempts or access control scenarios, providing a seamless authentication experience.
The process begins when an individual presents themselves to the system, which captures their facial image and creates a biometric template using the same methods employed during enrollment. The system then compares this template against the stored template associated with the claimed identity, calculating a similarity score. If the score exceeds the configured threshold, the check succeeds and the individual gains access.
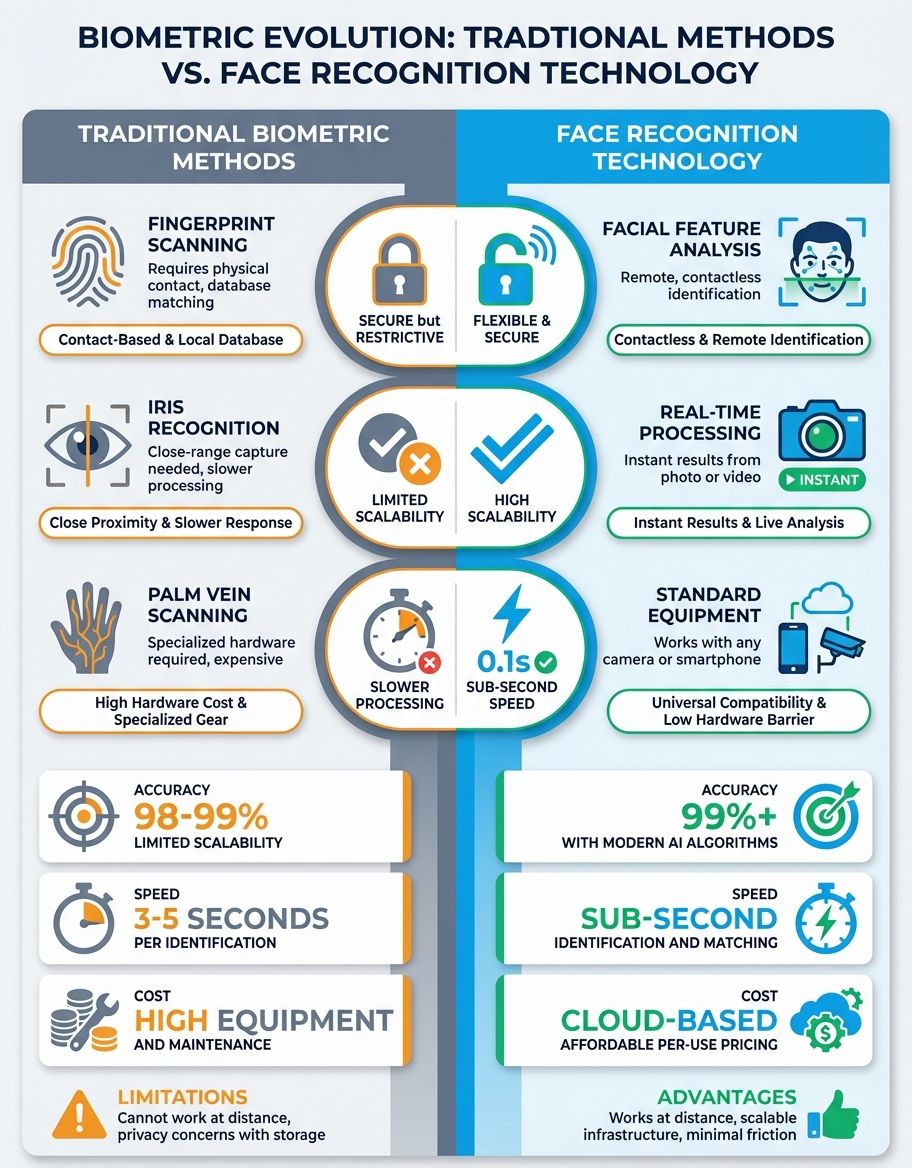
Applications extend across numerous domains, from financial services using face recognition for customer onboarding to healthcare facilities confirming patient status. The nature of facial authentication offers advantages over traditional methods, as faces cannot be easily forgotten, lost, or shared like passwords or access cards. This inherent connection between the person and their template provides robust security for authentication scenarios.
Advanced systems incorporate anti-spoofing measures detecting presentation attacks using photographs or videos. Liveness detection confirms the subject is physically present, analyzing characteristics like subtle facial movements, skin texture, or three-dimensional depth information. These safeguards ensure the process resists common attack vectors, maintaining security integrity across diverse deployment environments.
Technical Implementation of Biometric Technology
The methods powering this technology represent the culmination of decades of research in computer vision, pattern recognition, and machine learning. Early systems relied on geometric approaches measuring distances between facial landmarks, while modern technology employs deep learning neural networks that can identify complex patterns invisible to traditional methods. These sophisticated approaches analyze facial features at multiple scales, extracting representations that remain stable across variations in lighting, expression, and aging.
Convolutional neural networks have revolutionized biometric accuracy, learning hierarchical feature representations through training on massive datasets containing millions of facial images. These models develop an understanding of facial structure that enables them to generalize to new faces not seen during training. This learned approach surpasses hand-crafted feature extraction methods, achieving recognition accuracy that often exceeds human capabilities in controlled conditions.
The technical implementation of these systems involves multiple processing stages, each employing specialized methods. Face detection methods locate faces within images, often using technology like Haar cascades or more recent deep learning approaches. Alignment processes normalize facial position and scale, ensuring consistency for subsequent feature extraction. The feature extraction stage applies the core recognition methods, converting the aligned face into a compact template suitable for comparison.
Matching processes compare templates using distance metrics, calculating similarity scores that determine whether two templates represent the same individual. These systems must balance sensitivity and specificity, minimizing both false matches and false rejections. Ongoing research focuses on improving accuracy across diverse populations, addressing bias concerns, and enabling recognition from challenging capture conditions like partial occlusion or extreme poses.
Protection Against Misuse and Ethical Deployment
Protection against potential misuse of facial recognition requires comprehensive governance frameworks addressing both technical and policy dimensions. Organizations deploying the technology must implement safeguards preventing unauthorized use, ensuring systems serve only their intended purposes. Technical protections include access controls limiting who can query facial recognition systems and audit mechanisms tracking all usage for accountability.
The risk of misuse extends beyond direct security breaches to include function creep, where systems deployed for one purpose gradually expand to additional uses without proper oversight. Clear policies defining acceptable use cases and restrictions help prevent such expansion, while governance structures enforce these limitations. Regular reviews ensure ongoing compliance with established guidelines and identify emerging risks requiring additional protections.
Bias in biometric technology represents a significant concern, with studies demonstrating varying accuracy rates across different demographic groups. Safeguarding against such bias requires careful attention, training systems on diverse datasets and validating performance across population segments. Organizations must understand their systems' limitations and implement appropriate measures where accuracy concerns exist.
Ethical deployment frameworks guide responsible facial recognition implementation, emphasizing principles like transparency, consent, and proportionality. Organizations should clearly communicate when and how they use facial recognition, providing individuals with meaningful information about data collection and use. Limiting deployment to scenarios where facial recognition provides substantial benefits proportionate to privacy impacts helps ensure ethical use of this powerful technology.
Comparison Table: Facial Recognition Application Domains
| Application Domain | Primary Use Case | Key Benefit | Security Level | Privacy Consideration |
|---|---|---|---|---|
| Financial Services | Customer identity verification and fraud prevention | Reduces identity theft and streamlines account access | High | Requires explicit consent and secure storage |
| Law Enforcement | Suspect identification and surveillance | Accelerates criminal investigations | Critical | Significant privacy concerns in public spaces |
| Access Control | Physical and logical access to secured facilities | Contactless authentication improves convenience | Medium to High | Limited to enrolled users in controlled environments |
| Healthcare | Patient identification and medical record access | Prevents medical errors and ensures accurate treatment | High | Protected health information requires HIPAA compliance |
| Consumer Electronics | Device unlocking and personalization | User convenience and device security | Medium | Data stored locally on device reduces cloud risks |
| Retail | Customer recognition and personalized experiences | Enhanced customer service and marketing insights | Low to Medium | Opt-in models preferred to respect shopper privacy |

Frequently Asked Questions
How does the system verify identity using facial features?
The system verifies identity by capturing a person's face, analyzing unique features like eye spacing and jaw shape, then comparing the resulting template against stored records. When the similarity score exceeds the configured threshold, the system confirms the person's identity. This verification process happens in seconds, providing rapid authentication while maintaining security through sophisticated matching algorithms that detect subtle facial characteristics.
How does matching work in facial recognition systems?
Matching works by comparing two facial templates using mathematical algorithms that calculate similarity scores. The system measures the distance between feature vectors representing each face, with smaller distances indicating higher similarity. One-to-one matching verifies a claimed identity, while one-to-many matching identifies an unknown person by searching the entire database. Advanced matching techniques account for factors like aging, facial expressions, and image quality to maintain accuracy across real-world conditions.
How does the technology analyze facial images?
The technology analyzes facial images through multiple processing stages, beginning with face detection to locate faces within images. Algorithms then identify facial landmarks like eye corners, nose tip, and mouth edges, creating a geometric map of facial structure. Deep learning models extract feature representations capturing both obvious and subtle facial characteristics. This multi-layered analysis produces a compact template representing the unique aspects of each person's face suitable for rapid comparison.
How does capturing work in face recognition systems?
Capturing works through optical sensors like cameras that acquire digital images or video frames containing faces. The system uses software to detect when a face appears in the camera's field of view, automatically triggering the capture process. Quality assessment algorithms evaluate captured images, ensuring sufficient resolution, proper lighting, and minimal blur before proceeding with template creation. Some systems provide feedback guiding users to position themselves optimally, improving capture quality and subsequent recognition accuracy.
How does a digital image convert to biometric data?
A digital image converts to biometric data through specialized algorithms that extract facial features from pixel information. The software processes the image to identify facial landmarks, measuring distances and angles between key points. These measurements, along with texture analysis and deep learning feature extraction, create a numerical template representing the face. This biometric template typically contains several hundred to thousands of data points, forming a compact representation much smaller than the original image while preserving essential identifying information.
How does using software improve recognition accuracy?
Using software improves recognition accuracy by applying sophisticated algorithms that can detect subtle facial patterns invisible to human observers. Machine learning models trained on millions of faces learn to identify distinguishing features robust to variations in lighting, angle, and expression. Software can also implement quality controls, rejecting poor captures and requesting better images, while advanced techniques like multi-frame fusion combine information from multiple captures to produce more reliable templates. Continuous software updates incorporate the latest algorithmic improvements, progressively enhancing accuracy over time.
How does comparing two face images determine identity?
Comparing two face images determines identity by first converting each image into a biometric template using the same feature extraction algorithms. The system then calculates a similarity score measuring how closely the templates match, typically using distance metrics in high-dimensional feature space. If this score exceeds a predetermined threshold, the system concludes the images represent the same person. The threshold setting balances security against usability, with higher thresholds reducing false matches while potentially increasing false rejections of legitimate users.
