Face Recognition Tools: Facial Recognition Technology for Security
Your comprehensive guide to advanced facial recognition technology for enterprise security and identity management.
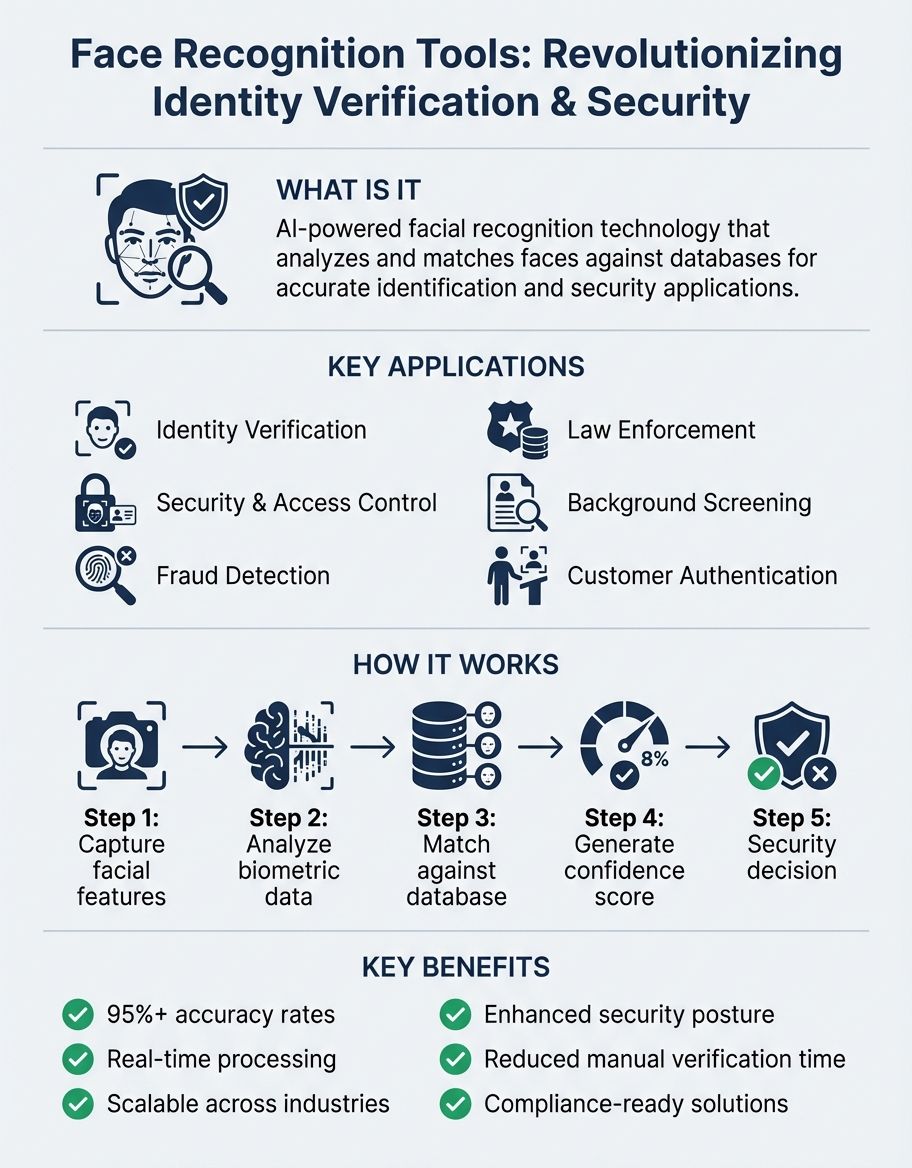
Face recognition tools have revolutionized how businesses verify identity and enhance security across multiple industries. These advanced systems use facial recognition technology to analyze and match faces against databases, providing accurate detection and authentication. Whether you're implementing security measures, streamlining access control, or protecting sensitive data, understanding how these tools work is essential for modern businesses.
Understanding Facial Recognition in Face Recognition Tools
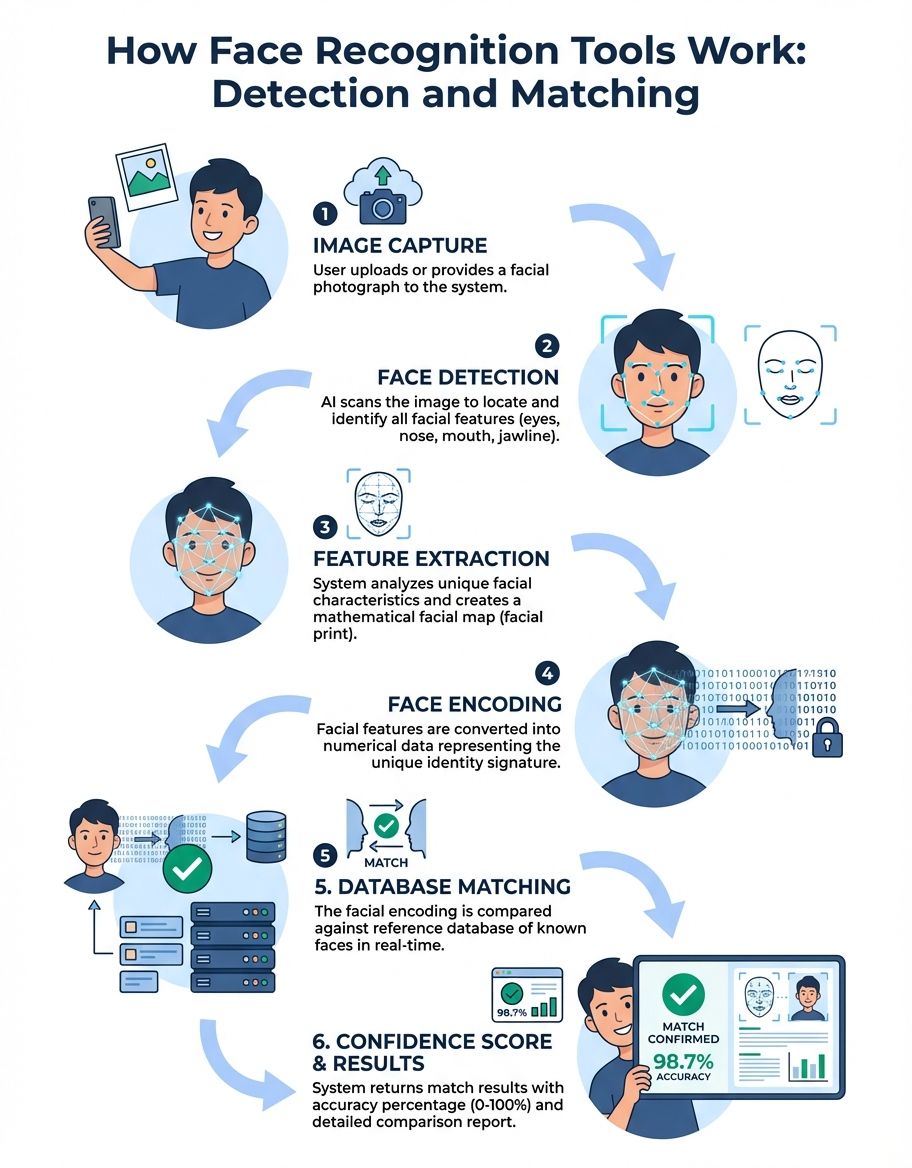
Facial recognition is the core technology that powers modern face recognition tools. These systems capture and analyze unique facial features to create biometric templates that can be matched against stored data. The facial recognition process involves multiple steps, from initial detection to final verification, ensuring accurate identification of individuals. To learn more about the technical processes behind these systems, check out our detailed explanation of how face recognition technology works.
Advanced facial recognition technology uses machine learning algorithms to improve accuracy over time. The software analyzes geometric patterns, spatial relationships between facial features, and unique characteristics that distinguish one person from another. This level of precision makes facial recognition one of the most reliable biometric authentication methods available for businesses today. For a comprehensive overview of face recognition systems and applications, explore our face recognition guide.
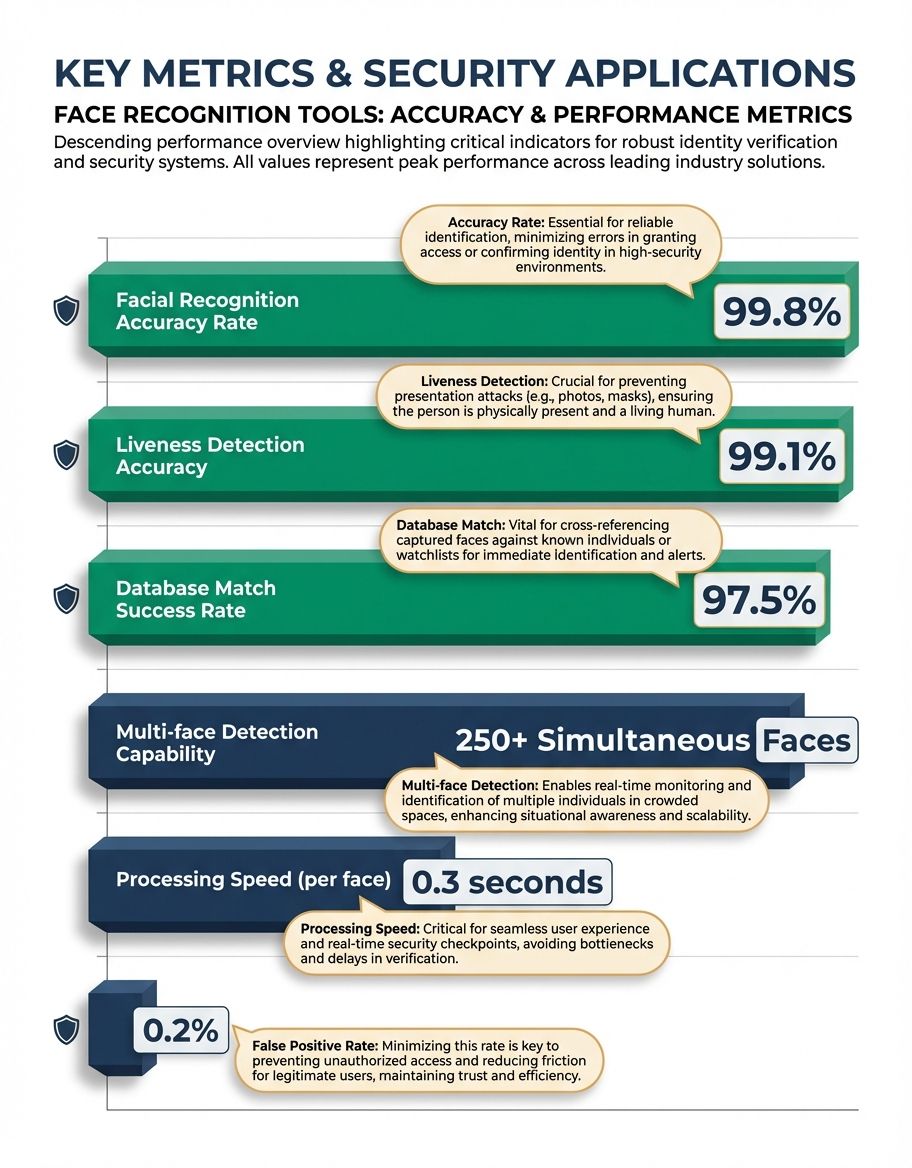
Modern facial recognition systems can process thousands of faces per second, making them ideal for high-traffic environments. Law enforcement agencies, retail businesses, and security firms rely on facial recognition to identify individuals quickly and accurately. The technology continues to evolve, with improvements in detection speed and accuracy reducing false positives.
The integration of facial recognition technology into existing security infrastructure provides seamless authentication. Businesses can implement these tools without disrupting current workflows, as the systems work in the background to verify identity and grant access based on pre-defined security parameters.
Understanding Image Recognition in Face Recognition Tools
Image recognition capabilities extend beyond simple facial detection to analyze entire visual datasets. Face recognition tools use sophisticated image recognition algorithms to extract meaningful information from photographs, surveillance footage, and live video streams. This technology enables platforms to identify not just faces, but also contextual elements that enhance overall security.
Advanced image recognition ensures that face recognition tools maintain accuracy even in challenging lighting conditions and complex environments.
The image recognition component processes visual data by breaking down images into analyzable segments. These platforms can detect faces in various lighting conditions, angles, and resolutions, making them versatile for real-world applications. Advanced image recognition ensures that face recognition tools maintain accuracy even in challenging environments.
Machine learning models trained on millions of images enable these platforms to recognize patterns and anomalies. The image recognition technology works alongside detection mechanisms to filter out irrelevant data and focus on facial features that matter for identification purposes. This targeted approach improves processing speed and reduces computational overhead.
Understanding Detection in Face Recognition Tools
Detection mechanisms form the foundation of any effective face recognition system. The detection phase identifies the presence of faces within images or video streams, marking regions of interest for further analysis. This critical step determines whether facial recognition processing should occur and where processing resources should be allocated.
Modern detection algorithms can identify multiple faces simultaneously, even in crowded environments. The detection technology accounts for variations in pose, expression, and partial occlusions that might obscure facial features. Advanced detection capabilities ensure that face recognition tools maintain performance across diverse scenarios.
Real-time detection enables security platforms to respond immediately to potential threats, processing video feeds continuously and triggering alerts when unauthorized individuals appear.
Real-time identification enables security platforms to respond immediately to potential threats. The technology processes video feeds continuously, triggering alerts when unauthorized individuals are detected or when known persons of interest appear. This proactive identification approach enhances overall security posture for businesses.
Identification accuracy directly impacts the effectiveness of facial recognition platforms. High-quality identification algorithms minimize false negatives while maintaining rapid processing speeds. The balance between identification sensitivity and specificity ensures that face recognition tools deliver reliable results without overwhelming security personnel with false alarms.
Integration of liveness identification prevents spoofing attempts using photographs or masks. Advanced identification mechanisms verify through liveness checks that the subject is a living person. These liveness measures rather than a static image, adding an extra layer of security to facial recognition processes.
Understanding Protection in Face Recognition Tools
Protection represents the primary benefit of implementing face recognition tools in business environments. These platforms provide multi-layered protection through biometric authentication, access control, and continuous monitoring. The protection advantages extend beyond traditional password-based platforms, offering higher resistance to unauthorized access attempts.
Face recognition tools enhance physical protection by controlling entry to restricted areas. Organizations can implement these platforms at entry points, server rooms, and sensitive facilities to ensure only authorized personnel gain entry. The protection measures operate automatically, reducing reliance on manual verification processes.
Data protection remains paramount in facial recognition implementations. Modern face recognition tools encrypt biological templates and transmission data, protecting sensitive information from interception or theft. The protection protocols comply with privacy regulations while maintaining system effectiveness.
Cybersecurity features protect facial recognition databases from unauthorized entry. Multi-factor authentication, encryption standards, and regular protection audits ensure that stored biological data remains protected. These protection measures prevent database breaches that could compromise identity information.
Real-time protection monitoring enables immediate response to threats. Recognition software can integrate with existing protection infrastructure, triggering alarms, locking doors, or alerting personnel when suspicious activity is detected. This proactive protection approach minimizes response times during critical incidents.
Compliance with protection standards ensures that face recognition implementations meet industry requirements. Organizations implementing these tools must address privacy concerns while leveraging protection benefits. Transparent protection policies and proper consent mechanisms balance technological capabilities with ethical considerations.
The protection framework includes audit trails that track all system activities. These logs provide accountability and enable forensic analysis when protection incidents occur. Comprehensive protection documentation supports regulatory compliance and demonstrates due diligence in protecting biological information.
Understanding Businesses Using Face Recognition Tools

Businesses across multiple sectors have adopted face recognition tools to streamline operations and enhance protection. Retail organizations use these platforms for customer analytics, personalized marketing, and theft prevention. The technology helps organizations understand customer behavior patterns while protecting against protection threats.
Financial institutions implement facial recognition for secure customer authentication at ATMs and branch locations. These organizations leverage biological technology to reduce fraud while improving customer experience. The seamless authentication process eliminates the need for physical cards or PINs, enhancing convenience for customers.
Healthcare organizations utilize face recognition tools to verify patient credentials and protect medical records. The tech solutions ensures that sensitive health information remains accessible only to authorized individuals, supporting HIPAA compliance requirements. Medical facilities benefit from improved protection without sacrificing patient care quality.
Tech solutions organizations develop and deploy advanced facial recognition software for various applications. These organizations create platforms that other organizations can integrate into their operations, democratizing entry to sophisticated biological tech solutions. Services range from simple API integrations to comprehensive protection solutions.
Manufacturing organizations implement face recognition for entry control in production facilities. The platforms track employee movements through secure areas, ensuring that only qualified personnel entry dangerous equipment or sensitive processes. This application enhances workplace safety while maintaining protection protocols.
Understanding Faces and Identification Accuracy
The ability to accurately analyze faces depends on sophisticated algorithms that measure facial geometry and unique characteristics. Face recognition tools evaluate multiple data points across faces, creating detailed biological profiles that enable reliable identification. The quality of facial analysis directly impacts system performance. You may also find our guide on face recognition biometrics helpful for understanding related approaches.
Variations in facial expressions, aging, and accessories present challenges for recognition platforms. Advanced tools account for these natural changes, maintaining accuracy even when faces display different emotions or include glasses and facial hair. The adaptability ensures long-term reliability as individuals' appearances evolve.
Multi-angle face capture improves recognition rates by collecting data from various perspectives. Platforms that analyze faces from different angles create more comprehensive biological templates, reducing the likelihood of failed matches. This thorough approach to capturing individuals enhances overall system effectiveness.
Processing speed for analyzing individuals has improved dramatically with modern hardware acceleration. Face recognition tools can evaluate hundreds of individuals per second, enabling real-time applications in high-traffic environments. The rapid processing ensures minimal delays in authentication workflows.
Understanding Images Processing and Storage
Efficient handling of images is crucial for face recognition platforms operating at scale. These tools must process, analyze, and store millions of images while maintaining quick retrieval times. Advanced image compression techniques reduce storage requirements without sacrificing recognition accuracy.
Image quality standards ensure that captured data meets minimum requirements for accurate face matching. Face recognition software often includes image enhancement features that improve lighting, contrast, and resolution before analysis. These preprocessing steps maximize the usable data extracted from images.
Database management platforms organize images for rapid searching and matching. Indexed storage structures enable face recognition tools to compare new images against vast databases in milliseconds. The efficient organization of photos supports scalability as organizations expand their biological databases.
Cloud storage solutions offer organizations flexibility in managing face matching photos. Recognition software provides secure, scalable storage with built-in redundancy and disaster recovery capabilities. Cloud-based image storage enables entry to recognition services from multiple locations while centralizing data management.
Retention policies govern how long photos remain in face recognition databases. Organizations must balance operational needs with privacy requirements when storing biological photos. Clear policies ensure compliance with regulations while maintaining system effectiveness.
Image analytics extract valuable insights beyond basic face matching. Advanced platforms analyze photos to detect emotions, estimate age ranges, and identify demographic information. These additional analytics help organizations understand their audiences while maintaining protection functions.
Metadata tagging organizes photos with contextual information that enhances searchability. Face recognition tools can associate photos with timestamps, locations, and event data, creating comprehensive records that support protection investigations and operational analysis.
Understanding Services and Tech Solutions Integration
Face recognition services encompass both cloud-based platforms and on-premises solutions. Cloud services offer rapid deployment without significant infrastructure investments, making the tech solutions accessible to organizations of all sizes. These services provide APIs that developers can integrate into applications with minimal coding.
Amazon Rekognition and similar services demonstrate how major tech solutions providers make face matching accessible. These platforms offer pre-trained models that organizations can use immediately, eliminating the need for extensive machine learning expertise. The services scale automatically to handle varying workloads.
Multi-modal biometric platforms combine facial recognition with fingerprint, iris, and voice authentication to create extremely secure enterprise authentication processes.
Integration solutions connect face recognition software with existing business platforms. APIs enable seamless data flow between recognition platforms and CRM platforms, entry control hardware, and protection management software. This integration creates unified protection ecosystems that leverage biological tech solutions alongside traditional measures.
The tech solutions underlying these solutions continues to advance, incorporating artificial intelligence and deep learning improvements. Regular updates enhance accuracy, reduce bias, and expand capabilities without requiring organizations to replace existing hardware. This evolutionary approach protects tech solutions investments.
Managed solutions allow organizations to outsource face matching operations to specialized providers. These solutions handle system maintenance, protection updates, and performance optimization, freeing internal teams to focus on core business activities. The expertise of service providers ensures optimal system performance.
Biological tech solutions integration extends beyond face matching to include fingerprint scanning, iris recognition, and voice authentication. Multi-modal biological platforms combine these technologies to create extremely secure authentication processes. The integration of multiple biological factors reduces vulnerability to spoofing attacks.
Credentials management platforms incorporate face matching as part of comprehensive authentication frameworks. These platforms manage user credentials across multiple applications and solutions, using facial biometrics as a convenient and secure authentication factor. The centralized credentials management simplifies entry control across organizations.
Tech Solutions Comparison: Face Recognition Software

| Feature | Cloud Solutions | On-Premises Platforms | Hybrid Solutions |
|---|---|---|---|
| Deployment Speed | Immediate (API entry) | Weeks to months | Days to weeks |
| Initial Cost | Low (subscription) | High (hardware/software) | Medium (mixed model) |
| Scalability | Automatic scaling | Manual capacity planning | Flexible scaling options |
| Data Control | Provider managed | Full local control | Configurable control |
| Maintenance | Provider handles updates | Internal IT responsibility | Shared responsibility |
| Customization | Limited to API features | Fully customizable | Moderate customization |
| Performance | Network dependent | Local processing speed | Optimized routing |
Frequently Asked Questions
How does face search work with recognition tools?
Face search functionality enables users to upload a photograph and search databases for matching individuals. The recognition tools analyze the submitted image, extract facial features, and compare them against stored biological templates. Advanced algorithms rank results by similarity, presenting the most likely matches first. This tech solutions powers reverse image search capabilities and helps locate individuals across large databases quickly and accurately.
How does search by image extension work?
Search by image extensions integrate face matching directly into web browsers, allowing users to right-click any photograph and initiate a face search. These extensions connect to face matching solutions through APIs, submitting the image for analysis and returning matching results from various databases. The extensions simplify the search process, making powerful recognition tech solutions accessible through familiar browser interfaces without requiring specialized software installations.
How does Amazon Rekognition work?
Amazon Rekognition is a cloud-based face matching service that uses deep learning models to analyze photos and video. The service processes uploaded content through neural networks trained on millions of individuals, identifying individuals, detecting emotions, and estimating demographic attributes. Rekognition provides API entry that developers integrate into applications, enabling face matching capabilities without managing infrastructure. The service scales automatically and continuously improves through machine learning updates.
How does MediaPipe face detector task work?
MediaPipe face detector task is an open-source framework that performs real-time facial identification on devices. The tech solutions uses lightweight machine learning models optimized for mobile processors, enabling face identification without cloud connectivity. MediaPipe analyzes video frames to locate individuals, track movements, and identify facial landmarks for augmented reality applications. The on-device processing with liveness validation ensures privacy while delivering rapid identification suitable for interactive applications.
How does face picture search work?
Face picture search analyzes uploaded photographs to identify and match individuals against databases. The platforms extract biological features from the picture, convert them into searchable data points, and query databases for similar facial patterns. Advanced matching algorithms account for variations in lighting, angles, and image quality to return accurate results. The tech solutions enables both one-to-one verification (confirming a specific credentials) and one-to-many identification (finding a person across multiple photos).
What is PimEyes and how does it work?
PimEyes is a face matching search engine that scans publicly available photos across the internet. Users upload a photograph, and the system searches websites, social media platforms, and image databases for matching individuals. The tech solutions raises privacy concerns as it reveals where someone's photos appear online without requiring their consent. While useful for monitoring personal digital footprints, the service demonstrates both the power and potential privacy implications of face matching tech solutions.
How does photo search engine tech solutions work?
Photo search engines use computer vision and face matching to analyze and categorize photos. When users submit a query photo, the engine extracts visual features, including individuals, objects, and scenes. The system compares these features against indexed photos, returning visually similar results. Advanced engines combine face matching with contextual understanding, identifying not just who appears in photos but also where photos were taken and what activities they depict. This comprehensive analysis enables sophisticated image retrieval capabilities.
How does Clearview AI differ from other face recognition software?
Clearview AI has compiled one of the largest face matching databases by scraping billions of photos from public websites and social media platforms. Law enforcement agencies use the tech solutions to identify suspects by comparing crime scene photos against this massive database. Unlike consumer solutions, Clearview AI focuses on investigative applications, providing tools specifically designed for law enforcement workflows. The platform's extensive database and powerful matching algorithms make it controversial yet effective for criminal investigations.
Securing Your Future with Face Recognition Tools
Face recognition tools represent a transformative leap in security technology, offering businesses unprecedented capabilities for identity verification, access control, and threat detection. As these platforms continue to evolve with advances in artificial intelligence and machine learning, organizations that adopt facial recognition today position themselves at the forefront of security innovation.
Whether you're seeking to enhance physical security, streamline authentication processes, or comply with regulatory requirements, modern face recognition tools deliver the accuracy, speed, and reliability essential for enterprise operations. By understanding the technology's capabilities and implementing best practices for privacy and data protection, your organization can harness the full potential of facial recognition while maintaining ethical standards and user trust.
