CaraComp - The #1 AI Face Comparison Tool
Advanced facial recognition technology for modern investigations and identity verification.

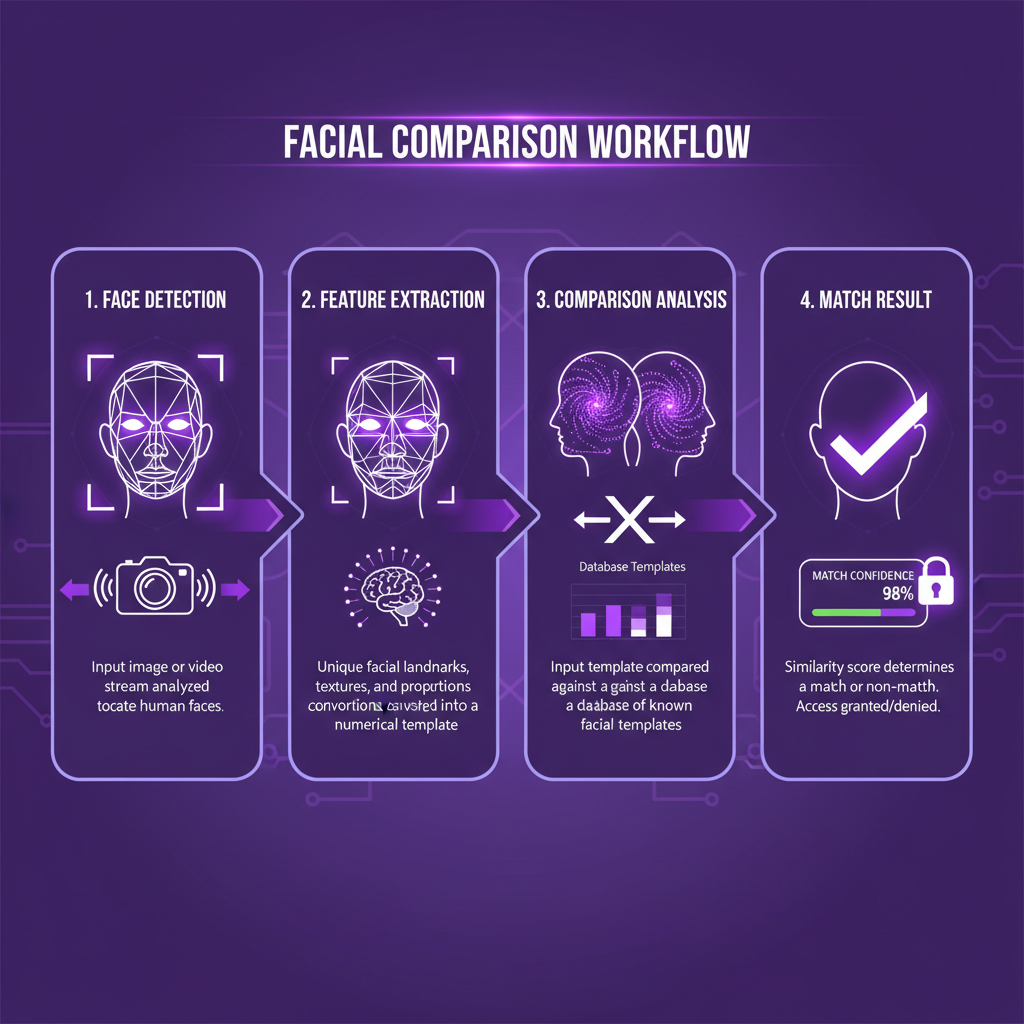
At its core, facial comparison technology analyzes image data by extracting unique facial features from photos and creating mathematical representations called facial templates. When you upload an image, the system identifies key landmarks on the person's face including the distance between eyes, nose shape, jawline contours, and cheekbone structure. These facial measurements are converted in Explore all our tools at CaraComp.
Security Applications of Facial Comparison
Security professionals rely on facial comparison technology to protect facilities, verify identities, and prevent unauthorized access. Access control systems use this technology to compare live photos of individuals against authorized personnel databases, granting entry only when a match is confirmed. This application has become standard in high-security environments including government buildings, data centers, and financial institutions where traditional badge-based systems can be compromised through theft or sharing. Law enforcement agencies use facial comparison for identification and screening during investigations. Officers can upload photos from security cameras or public sources and compare them against databases of persons of interest. The technology helps identify suspects, locate missing persons, and verify identities during field encounters. Real-time facial comparison enables security teams to receive instant alerts when individuals matching watchlist criteria appear in monitored areas. Border security and immigration control represent critical applications where facial comparison enhances both security and efficiency. Automated screening systems compare traveler photos against passport images and watchlist databases, flagging discrepancies for human review. This layered approach combines the speed of automated facial comparison with human judgment, reducing wait times while maintaining rigorous security standards for identity verification at international checkpoints. Financial institutions increasingly adopt facial comparison for fraud prevention and customer verification. When users upload identity documents during account opening, the technology compares the photo on the document against a selfie taken during the enrollment process. This security measure prevents identity theft and ensures the person opening the account is who they claim to be, protecting both the institution and legitimate customers from fraudulent activity. For more details, check out our guide on face similarity test.
Upload and Compare Photos in Real Time
Modern facial comparison platforms make it simple to upload photos and receive instant analysis results. Users can drag and drop images into web interfaces or submit photos through mobile applications for immediate processing. The system analyzes each image as soon as you upload it, extracting facial data and preparing it for comparison against other photos in your workflow. This real-time capability eliminates delays that would slow down time-sensitive security operations or identity verification processes. The upload process supports various image formats including JPEG, PNG, and HEIC files from smartphones and digital cameras. Advanced systems automatically detect and crop faces from larger photos, focusing the comparison on relevant facial regions while filtering out background elements. Users can upload multiple photos simultaneously for batch comparison, enabling efficient analysis of large image collections in security investigations or photo matching projects. Real-time comparison delivers results within seconds of uploading photos. The system displays similarity scores indicating how closely faces in different images match, often accompanied by visual overlays highlighting matched facial features. This immediate feedback allows security personnel to make rapid decisions about identity verification or access control without waiting for manual review or offline processing of photo data. Cloud-based platforms enable real-time facial comparison from any location with internet access. Security teams can upload photos from mobile devices in the field and instantly compare them against centralized databases. This distributed capability extends facial comparison beyond fixed installations, supporting dynamic security operations where officers need immediate identity verification during patrols, checkpoints, or emergency response situations involving person identification from uploaded images. Get started with face similarity testing using our face similarity test tool.
Facial Recognition vs Facial Comparison: Understanding the Differences
While often used interchangeably, facial recognition and facial comparison represent distinct technological approaches with different capabilities and use cases. Facial recognition identifies a specific person by matching their face against a database of known individuals, answering the question "Who is this person?" In contrast, facial comparison determines whether two facial images show the same person, answering "Are these the same individual?" Understanding this distinction helps organizations select the appropriate technology for their security and identity verification requirements. Facial recognition systems maintain large databases of identity templates linked to personal information. When the system captures an image of a person, it searches the entire database attempting to find a match and identify the individual. This one-to-many matching process requires significant computational resources and raises privacy considerations, as it involves storing and searching facial data for numerous people. Government agencies and large corporations typically deploy facial recognition for access control and security monitoring. Facial comparison operates on a simpler one-to-one or one-to-few matching model. Users provide two or more specific images and the system determines if they show the same person without needing to search large databases. This focused approach offers advantages for identity verification scenarios where you already have reference photos - such as comparing a live photo against a passport image or verifying that an uploaded selfie matches an ID card. The limited scope of facial comparison reduces both computational requirements and privacy concerns. Both technologies analyze facial features and create mathematical templates for matching, but their architectural differences lead to distinct performance characteristics. Facial recognition must maintain high accuracy across potentially millions of identity templates, requiring extensive computational infrastructure. Facial comparison systems can achieve high accuracy with simpler deployments since they only compare a limited set of images at a time. This makes facial comparison more accessible for organizations that need identity verification without the complexity of full facial recognition infrastructure.
While often used interchangeably, facial recognition and facial comparison represent distinct technological approaches with different capabilities and use cases.
Developer Integration and API Access
Software developers can integrate facial comparison capabilities into applications through APIs that provide programmatic access to image analysis technology. These APIs accept photo uploads via HTTP requests and return comparison results as structured data, enabling seamless incorporation of facial analysis into custom workflows. Developers benefit from abstracting the complex mathematics of facial comparison behind simple API calls that require minimal code to implement in applications. Modern facial comparison APIs support both synchronous and asynchronous processing models. Synchronous APIs return comparison results immediately within the same request-response cycle, ideal for real-time applications where users expect instant feedback after uploading photos. Asynchronous APIs accept image uploads and process them in the background, sending results via webhooks when analysis completes. This approach suits high-volume batch processing where immediate results aren't required but efficient resource utilization is important. Developer documentation typically includes code samples demonstrating how to upload images, initiate comparisons, and parse results in popular programming languages. SDKs for JavaScript, Python, Java, and other languages simplify integration by providing pre-built functions that handle authentication, data formatting, and error handling. These tools accelerate development cycles and reduce the technical barriers to incorporating facial comparison technology into security applications, identity verification systems, and photo management platforms. Enterprise-grade APIs include features supporting production deployments at scale. Rate limiting controls protect infrastructure while ensuring fair resource allocation across multiple clients. Webhook configurations enable event-driven architectures where applications receive automatic notifications when comparison results are ready. Detailed logging and analytics help developers monitor API usage, track performance metrics, and troubleshoot integration issues. These developer-focused capabilities make facial comparison technology accessible even to teams without specialized expertise in computer vision or image processing algorithms.

The Future of Facial Comparison Technology
Emerging advancements in facial comparison technology promise even greater accuracy, speed, and applicability across diverse use cases. Machine learning models continue evolving, with newer algorithms achieving human-level or better performance on challenging image datasets. These improvements extend facial comparison capabilities to scenarios previously considered too difficult, such as matching extremely low-quality surveillance photos or comparing faces captured under varied lighting conditions that defeated earlier systems. Integration with other biometric modalities will enhance security for critical applications. Multi-modal systems combine facial comparison with fingerprint, iris, or voice analysis, requiring matches across multiple biometric factors before confirming identity. This layered approach dramatically reduces false acceptance rates while maintaining user convenience, as facial comparison serves as a primary screening mechanism with other biometrics confirming high-confidence matches. Organizations deploying these systems gain flexibility to adjust security levels based on risk, using facial comparison alone for routine transactions while requiring additional factors for sensitive operations. Privacy-preserving facial comparison techniques address growing concerns about surveillance and data protection. Homomorphic encryption enables comparison of encrypted facial templates without decrypting them, protecting person identity throughout the process. Federated learning approaches train facial comparison models without centralizing image data, allowing organizations to benefit from improved technology while maintaining control over sensitive photos. These innovations will expand facial comparison adoption by resolving the tension between security benefits and privacy risks. Edge computing brings real-time facial comparison to devices without requiring cloud connectivity. Processing image analysis locally on smartphones, security cameras, or embedded devices eliminates latency and network dependencies while enhancing privacy by keeping photos on-device. This distributed architecture will enable new applications where cloud upload isn't feasible or desirable, from offline identity verification in remote locations to instant photo matching in consumer applications that users control completely. As edge processors grow more powerful, local facial comparison technology will deliver cloud-equivalent accuracy with superior responsiveness and data protection.
