Face Recognition System: Biometric Security & Authentication Technology
Advanced biometric technology that verifies identity through facial analysis—securing access, preventing fraud, and transforming authentication across industries.
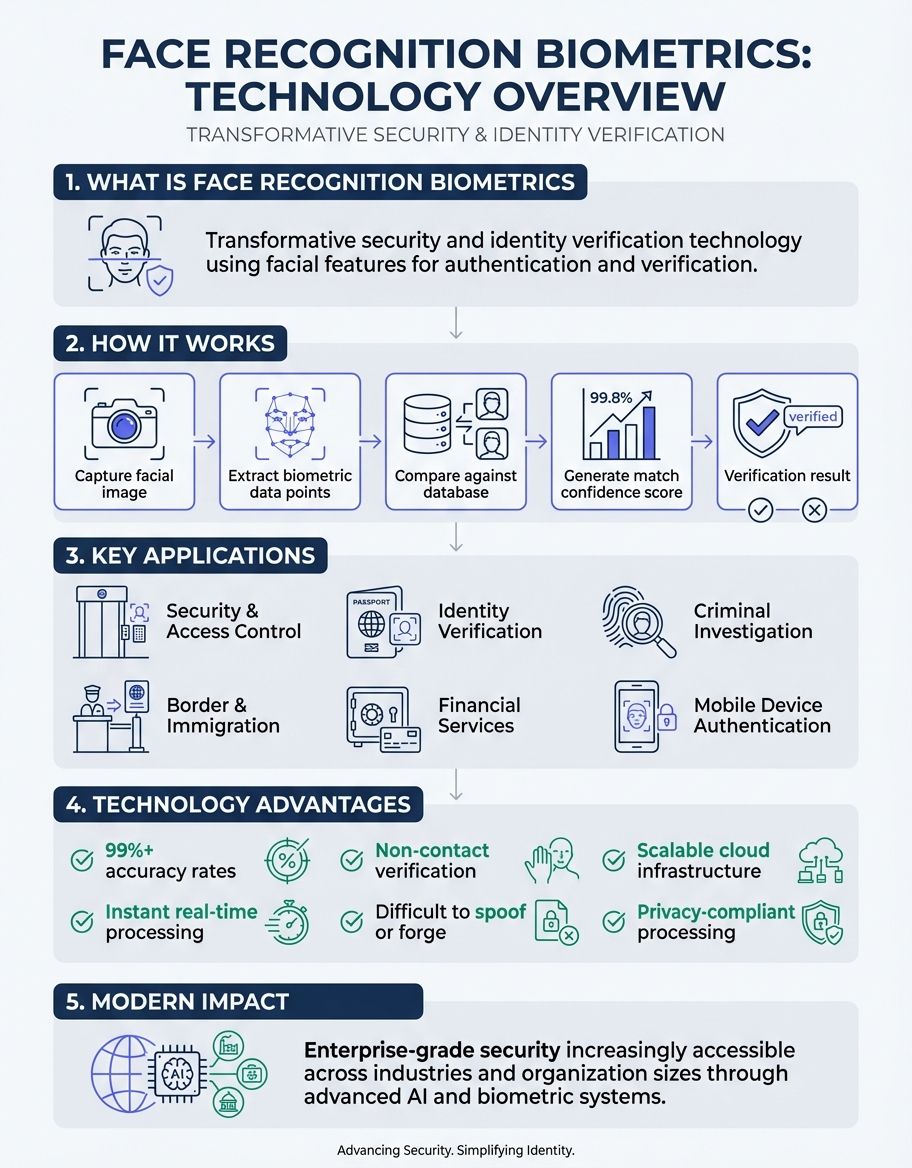
Face recognition biometrics represents one of the most transformative developments in modern security and identity verification technology. Organizations worldwide are ditching outdated authentication methods for facial recognition—and for good reason. This biometric verification method analyzes unique facial features to confirm a person's identity with remarkable accuracy, offering a secure alternative to passwords and PINs. For a comprehensive overview of face recognition technology, explore our face recognition guide.
The integration of face recognition biometrics into everyday access management systems has revolutionized how businesses, governments, and institutions approach security. From airport security checkpoints to smartphone unlocking, facial recognition technology has become ubiquitous. This technology captures and analyzes facial characteristics to create a digital template that serves as a unique identifier for each person. The data collected through this process enables organizations to implement robust verification protocols that significantly reduce fraud while streamlining the login process.
Understanding how face recognition biometrics works is essential for anyone interested in modern security solutions. Unlike passwords or physical tokens that can be stolen or forgotten, biometric verification relies on hard biometrics—permanent biological characteristics that are virtually impossible to replicate. The facial area contains numerous distinctive features that recognition systems can measure and compare, making it an ideal candidate for secure identity verification in both physical and digital environments.
Understanding Facial Recognition in Face Recognition Biometrics
Facial recognition technology forms the cornerstone of face recognition biometrics, utilizing sophisticated algorithms to identify individuals based on their unique facial features. The process begins when a camera captures an image of a person's face, which the system then analyzes to identify key facial landmarks such as the distance between eyes, nose shape, jawline contour, and other distinguishing characteristics. These measurements are converted into a mathematical representation that serves as the individual's biometric template.

The accuracy of facial recognition depends heavily on the quality of the captured image and the sophistication of the underlying technology. Modern recognition systems employ machine learning and artificial intelligence to continuously improve their ability to identify individuals under varying conditions, including different lighting scenarios, angles, and even with partial facial obstructions. This adaptability makes facial recognition particularly valuable for real-world applications where perfect conditions cannot always be guaranteed.
Organizations implementing facial recognition must consider several factors to ensure optimal performance. Environmental conditions, camera quality, database size, and processing power all influence the system's effectiveness. Additionally, the technology must balance speed with accuracy—verification needs to occur quickly enough to avoid bottlenecks while maintaining sufficient precision to prevent unauthorized access. When properly configured, facial recognition can achieve verification rates exceeding 99% accuracy, making it one of the most reliable biometric methods available.
The evolution of facial recognition has been remarkable. Early systems required subjects to remain stationary in controlled lighting, but today's technology can identify individuals in crowded environments, from video feeds, and even when the person is in motion. This advancement has expanded the potential applications beyond simple access control to include advanced security monitoring, customer experience enhancement, and fraud prevention across numerous industries. Explore our comprehensive guide on face recognition tools to discover the best solutions for implementing this technology.
Understanding Access Management in Face Recognition Biometrics
Access management represents a critical application of face recognition biometrics, enabling organizations to control who can enter physical spaces or access digital resources. Traditional access management relied on keys, cards, or passwords—all of which present safety vulnerabilities and administrative challenges. Face recognition biometrics transforms this paradigm by using each person's unique facial characteristics as their access credential, eliminating the need for physical tokens or memorized codes.
Implementing facial recognition for access control offers multiple advantages. The technology enables touchless authentication, which became particularly valuable during health crises when minimizing physical contact became a priority. Users simply approach a designated checkpoint, and the system automatically identifies them and grants or denies access based on their authorization level. This streamlined process reduces wait times, improves user experience, and minimizes the administrative burden of managing physical credentials.
Organizations across various sectors have adopted facial recognition for access control. Corporate offices use it to secure sensitive areas, ensuring only authorized personnel can enter restricted zones. Educational institutions employ the systems to monitor campus access and enhance student safety. Healthcare facilities leverage facial recognition to protect patient data and control access to medication storage areas. Each application demonstrates how biometric verification can address specific protection challenges while improving operational efficiency. You may also find our guide on benefits of face recognition systems helpful for understanding the organizational advantages of this technology.
For those seeking a reliable face comparison solution, CaraComp offers a powerful platform that combines advanced facial recognition technology with ease of use. Whether you're verifying identities, analyzing facial similarities, or implementing biometric authentication, CaraComp's technology delivers professional-grade results without the complexity. The platform processes images securely and provides instant, detailed comparison scores—making it an excellent choice for both casual users and security professionals alike.
The scalability of facial recognition-based access control makes it suitable for organizations of all sizes. Small businesses can implement basic systems to secure their premises, while large enterprises can deploy comprehensive networks that manage access across multiple locations. The platforms integrates seamlessly with existing secure systems infrastructure, allowing organizations to enhance their current systems without complete overhauls. As the technology continues to mature, entry control solutions are becoming more affordable and accessible to a broader range of users.
Understanding Verification in Face Recognition Biometrics
Verification stands at the heart of face recognition biometrics, serving as the fundamental process that confirms an individual's claimed identity. Unlike identification, which answers "who is this person?" verification addresses "is this person who they claim to be?" This distinction is crucial for understanding how facial recognition systems operate in different contexts. The verification process compares a newly captured facial image against a stored template to determine if they match with sufficient confidence.

The confirmation workflow begins when a person presents themselves to the system, typically by looking at a camera or sensor. The system captures their facial image and extracts relevant features, creating a temporary biometric template. This template is then compared against the stored template associated with the identity the person claims. The comparison generates a similarity score, and if this score exceeds a predetermined threshold, validation succeeds and the system confirms the person's identity.
Biometric verification through this confirmation method offers significant advantages over traditional methods. The process is rapid, often completing in less than a second, making it suitable for high-traffic environments where speed is essential. It provides a higher level of safety than passwords or PINs, which can be shared, stolen, or forgotten. Additionally, the systems validation creates an audit trail, recording each authentication attempt and its outcome, which proves invaluable for protection investigations and compliance requirements.
Here's the thing: organizations must carefully calibrate their confirmation systems to balance security with usability. Setting the similarity threshold too high may result in false rejections, frustrating legitimate users and potentially creating security gaps as frustrated individuals seek workarounds. Conversely, setting the threshold too low increases the risk of false acceptances, where unauthorized individuals gain access. Finding the optimal balance requires understanding the specific security requirements and user expectations of each deployment.
Advanced validation systems incorporate liveness detection to prevent spoofing attempts using photographs or videos. These anti-spoofing measures ensure that the system is verifying a live person rather than a representation of someone. Some systems request the user to perform specific actions, such as blinking or turning their head, while others use infrared sensors or depth cameras to confirm the physical presence of a real person. These additional layers of verification significantly enhance the overall security of the system.
Verification stands at the heart of face recognition biometrics, serving as the fundamental process that confirms an individual's claimed identity. Unlike identification, which answers "who is this pe...
Understanding Access in Face Recognition Biometrics
access control through face recognition biometrics has fundamentally changed how organizations manage entry to both physical and digital environments. The concept of entry encompasses more than simply allowing or denying entry—it involves creating sophisticated authorization frameworks that grant different levels of authorization based on individual roles, time of day, and specific safety requirements. facial recognition enables these nuanced access policies while maintaining ease of use and robust protection.
Physical entry applications of this confirmation method have become increasingly common in modern buildings and facilities. Entry gates, turnstiles, and doors equipped with the technology cameras can automatically grant authorization to authorized individuals while alerting security personnel to unauthorized entry attempts. This automated approach eliminates the delays associated with manual checks and reduces the possibility of human error in the verification. The solutions can also track movement patterns within a facility, providing valuable data for optimizing space utilization and identifying potential safety concerns.
electronic access represents another critical application of facial recognition systems. Mobile devices, computers, and cloud-based applications increasingly offer facial recognition method as an checks option. Users can unlock their devices or entry sensitive applications simply by looking at their camera, providing a seamless yet safe login experience. This approach significantly reduces the reliance on passwords, which remain one of the weakest links in virtual protection due to poor password practices and the vulnerability of credential databases to breaches.
The granularity of authorization control possible with the technology enables organizations to implement sophisticated security policies. Different individuals can have different access privileges, with some granted entry to all areas while others are restricted to specific zones. Time-based restrictions can automatically adjust entry permissions based on work schedules or business hours. Emergency protocols can instantly modify authorization rules in response to safety incidents, demonstrating the flexibility and responsiveness of modern biometric access systems.
Understanding Security in Face Recognition Biometrics
protection considerations permeate every aspect of face recognition biometrics, from the initial capture of facial images to the storage and protection of biometric templates. The solutions offers substantial security advantages over traditional login methods, but it also introduces unique challenges that organizations must address to maintain the integrity and trustworthiness of their biometric systems. Understanding these safety dimensions is essential for anyone implementing or relying on facial recognition systems.
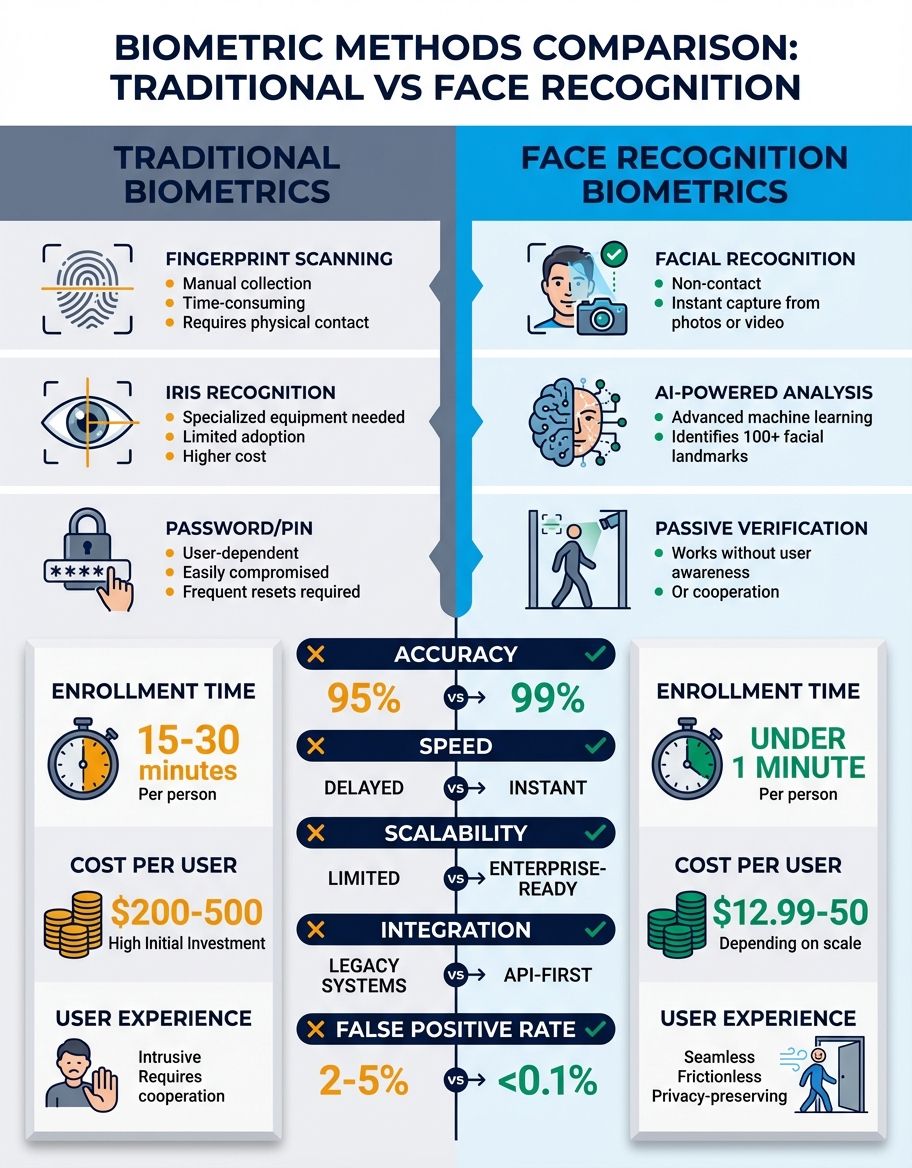
The inherent protection of biometric confirmation stems from the difficulty of replicating or stealing someone's facial characteristics compared to traditional credentials. While a password can be observed, guessed, or phished, and physical entry cards can be lost or stolen, a person's face remains with them at all times. This permanence creates a more safe foundation for authentication, particularly when combined with liveness detection that prevents the use of photographs or masks to fool the system.
However, the security of this validation method systems extends beyond the verification process itself. The storage and transmission of biometric data require robust protection measures to prevent unauthorized authorization or data breaches. Organizations must encrypt biometric templates both in transit and at rest, implement strict access controls for systems containing biometric data, and regularly audit their safety practices. The sensitive nature of biometric data—it cannot be changed if compromised like a password—makes these protective measures particularly critical.
Privacy concerns intersect significantly with protection in the technology applications. While the technology enhances security for many applications, it also raises questions about surveillance, consent, and the potential for misuse. Organizations implementing facial recognition must navigate these concerns by establishing clear policies regarding data collection, retention, and use. Transparency about how this confirmation method is employed and what safeguards protect individual privacy helps build trust and ensures compliance with evolving privacy regulations.
Ongoing safety maintenance represents another crucial aspect of the systems systems. Regular software updates address newly discovered vulnerabilities and improve recognition accuracy. protection audits identify potential weaknesses in system configuration or deployment. Incident response plans prepare organizations to handle potential security breaches or system compromises. This proactive approach to safety ensures that facial recognition systems remain effective and trustworthy throughout their operational lifetime.
Understanding Identity Verification in Face Recognition Biometrics
Identity validation through face recognition biometrics has revolutionized processes ranging from customer onboarding to border control. This application of the technology focuses on confirming that an individual is who they claim to be, typically by comparing their live facial image against a reference image from a trusted source such as a government-issued identification document. The process enables organizations to establish trust in online and physical interactions while reducing the time and resources required for manual verification.
The identity verification using this validation method typically involves multiple steps to ensure accuracy and prevent fraud. First, the individual provides a reference document such as a passport or driver's license. The system extracts the facial image from this document and analyzes its authenticity to detect potential forgeries. Next, the individual presents their face to a camera for a live capture. The system then compares this live image against the document photo, checking for a match while also performing liveness detection to ensure the person is physically present and not using a photograph or video.
Financial institutions have been early adopters of the technology for identity authentication, particularly for remote account opening and transaction authorization. The systems allows banks to onboard new customers without requiring in-person visits, significantly improving customer experience while maintaining regulatory compliance. When a customer applies for an account online, facial recognition verifies their identity by comparing their live selfie against their government ID, creating a protected and convenient verification that can be completed in minutes.
Government agencies use identity validation through facial recognition method for various purposes, including passport control, visa applications, and social services administration. At border crossings, the technology compares travelers' faces against their passport photos, expediting the verification while enhancing protection. This application has dramatically reduced wait times at immigration checkpoints while improving the accuracy of identity validation compared to manual inspection alone. The solutions helps identify individuals attempting to enter countries using fraudulent documents or stolen identities.
Identity validation through face recognition biometrics has revolutionized processes ranging from customer onboarding to border control. This application of the technology focuses on confirming that a...
Understanding Authentication in Face Recognition Biometrics
validation using face recognition biometrics provides a powerful alternative to traditional login methods such as passwords, PINs, and security tokens. The identity verification verifies that the person attempting to entry a system or service is genuinely authorized to do so by confirming their identity through facial analysis. This approach addresses many of the vulnerabilities inherent in knowledge-based and possession-based checks while offering superior user convenience.

The login workflow with facial recognition is remarkably simple from the user's perspective. Instead of typing a password or entering a code, the user simply positions their face within the camera's field of view. The system captures their facial image, extracts biometric features, and compares them against stored templates of authorized users. If a match is found, authentication succeeds and the user gains authorization to the requested resource. This frictionless process takes only seconds and requires no memorization or physical tokens.
Multi-factor confirmation increasingly incorporates facial recognition method as one of its factors, combining the safety of biometric confirmation with additional login elements. For high-protection applications, an organization might require both the systems and a password, or facial recognition and a physical security token. This layered approach provides defense in depth, ensuring that even if one authentication factor is compromised, the others maintain safety. The convenience of this validation method makes it an ideal component of multi-factor systems, as it doesn't add significant friction to the authentication. You may also find our guide on face recognition online helpful for understanding cloud-based solutions.
Mobile device login represents one of the most widespread applications of the technology solutions. Smartphone manufacturers have integrated sophisticated facial recognition systems that allow users to unlock their devices and authorize app access with a glance. These systems use specialized hardware, including infrared sensors and depth cameras, to create detailed facial maps that are extremely difficult to spoof. The convenience and protection of this authentication method have made it the preferred option for millions of users worldwide.
Understanding Data in Face Recognition Biometrics
Data management constitutes a fundamental aspect of face recognition biometrics, encompassing the collection, storage, processing, and protection of facial images and biometric templates. The effectiveness and security of any facial recognition method system depend heavily on how it handles this sensitive data throughout its lifecycle. Organizations must establish comprehensive data governance frameworks that address technical, legal, and ethical considerations while enabling the systems to function effectively.
The data collection phase begins when facial images are captured through cameras or sensors. The quality and consistency of this data significantly impact system performance. High-resolution cameras capture more facial detail, enabling more accurate recognition, while proper lighting ensures that facial features are clearly visible. Organizations must standardize their information collection processes to maintain consistency across different locations and scenarios. This standardization extends to factors such as camera positioning, image resolution, and environmental controls that influence capture quality.
Once captured, facial data undergoes processing to extract biometric features that form the basis for recognition. This processing converts the raw facial image into a mathematical template—a unique numerical representation of the individual's facial characteristics. These templates require significantly less storage space than full images while preserving the information necessary for accurate recognition. The transformation from image to template also enhances privacy, as the template cannot be reverse-engineered to recreate the original facial image.
biometric data storage and retention policies play a critical role in the technology systems. Organizations must determine how long to retain biometric data, where to store it, and what safety measures to implement. Encryption protects stored data from unauthorized entry, while authorization controls ensure that only authorized personnel can interact with the biometric database. Regular backups safeguard against biometric data loss, while robust deletion procedures ensure that information is properly destroyed when no longer needed. These practices must align with applicable data protection regulations and industry best practices.
The transmission of biometric biometric data between system components introduces additional protection considerations. Whether transferring information from capture devices to processing servers or synchronizing databases across multiple locations, organizations must protect data in transit using encryption and safe communication protocols. Network segmentation isolates biometric systems from other network traffic, reducing the attack surface and limiting potential exposure in the event of a network breach. These measures ensure that facial recognition biometric data remains protected throughout its journey through the organization's infrastructure.
Frequently Asked Questions
How does hard biometrics work?
Hard biometrics refers to permanent, physiological characteristics that remain stable throughout a person's life, such as facial structure, fingerprints, or iris patterns. Face recognition biometrics falls into this category because the fundamental bone structure and proportions of the face don't change significantly over time (even with aging). The system measures specific facial landmarks and their relationships to create a unique biometric template. These hard biometric traits cannot be easily altered or transferred between individuals, making them highly reliable for identity verification and security applications. The stability of these characteristics ensures that biometric templates remain valid for extended periods, though systems may request periodic re-enrollment to account for gradual aging or significant appearance changes.
How does unique facial features work?
Unique facial features are the distinctive characteristics that differentiate one person from another, including the distance between eyes, nose width and shape, cheekbone prominence, jawline contour, and dozens of other measurable points on the face. this validation method systems identify these features by analyzing facial images and locating specific landmarks. The system then measures the distances and angles between these landmarks to create a numerical representation of the face. Because each person has a unique combination of these features, the resulting biometric template serves as a reliable identifier. Even identical twins, who share similar overall facial structures, have subtle differences that sophisticated the technology systems can detect and use to distinguish between them.
How does analysing facial characteristics work?
Analysing facial characteristics involves sophisticated computer vision algorithms that process facial images to identify and measure distinctive features. The process begins with face detection, where the system locates the face within an image and determines its boundaries. Next, the algorithm identifies key facial landmarks such as the corners of the eyes, tip of the nose, and edges of the mouth. The system then measures the geometric relationships between these landmarks, including distances, angles, and proportions. Advanced systems also analyze texture patterns, such as skin characteristics and subtle variations in facial topology. Machine learning models combine all these measurements to create a comprehensive biometric template that captures the unique aspects of an individual's facial characteristics.
How does confirming a person's identity work?
Confirming a person's identity through face recognition biometrics involves comparing a newly captured facial image against a stored reference template to determine if they belong to the same individual. When someone claims a specific identity, the system retrieves the biometric template associated with that identity from its database. It then captures a live image of the person, extracts facial features, and creates a temporary template. The system compares these two templates using mathematical algorithms that calculate their similarity. If the similarity score exceeds a predetermined threshold, the system confirms the identity and grants access or approval. This process includes liveness detection to ensure the person is physically present and not using a photograph or video to deceive the system.
What role do biometrics play in modern security systems?
Biometrics serve as a cornerstone of modern safety systems by providing validation that cannot be easily stolen, shared, or forgotten. Face recognition biometrics specifically offers a balance of high protection and user convenience that makes it suitable for diverse applications. Organizations integrate biometric verification into multi-layered security frameworks that combine physical safety, electronic entry control, and identity management. The systems creates detailed audit trails that track who accessed what resources and when, supporting both protection operations and compliance requirements. As security threats evolve, biometric systems provide adaptive protection that can be updated and enhanced without requiring users to change their credentials or learn new procedures.
How does face recognition prevent fraud?
Face recognition biometrics prevents fraud by making it extremely difficult for unauthorized individuals to impersonate others or use stolen credentials. Unlike passwords or physical tokens that can be shared or stolen, a person's facial characteristics cannot be easily replicated or transferred. When combined with liveness detection, facial recognition systems can distinguish between a live person and photographs, videos, or masks, preventing common spoofing attempts. The platforms verifies identity at the point of transaction or authorization, ensuring that the person requesting access or authorization is physically present. This capability is particularly valuable in financial services, where this confirmation method helps prevent identity theft, account takeover, and fraudulent transactions by confirming that the legitimate account holder is initiating the action.
How does face biometrics integrate with existing security infrastructure?
Face biometrics integrates with existing safety infrastructure through standardized protocols and interfaces that allow different systems to communicate effectively. Modern the technology platforms offer APIs and SDKs that enable integration with entry control systems, visitor management platforms, time and attendance systems, and video surveillance networks. The systems can work alongside traditional login methods in hybrid configurations, where organizations gradually transition from legacy systems to biometric solutions. Integration often occurs at multiple levels: hardware integration connects facial recognition cameras to existing network infrastructure, software integration links biometric validation with identity management systems, and information integration synchronizes user databases across different platforms. This flexibility allows organizations to enhance their protection posture without completely replacing functional systems.
