Best biometric authentication app - protective capabilities & Services Review
Finding the best biometric authentication app requires understanding how these advanced security services leverage biometric information to verify identities. Modern face matching technology has evolved from simple photo matching to sophisticated systems that can identify individuals across millions of images with remarkable accuracy. Whether you're looking for personal protective capabilities or business-grade verification platforms, the landscape of face matching apps offers diverse solutions for every need.
The demand for secure face matching apps has grown exponentially as organizations and individuals seek reliable methods for verifying people's identities using their faces. From unlocking smartphones to accessing sensitive data, these apps have become integral to our daily digital interactions. Understanding the features, protective protocols, and information handling practices of leading facial identification platforms helps users make informed decisions about which app best serves their specific requirements.
Understanding face matching technology in Modern Apps
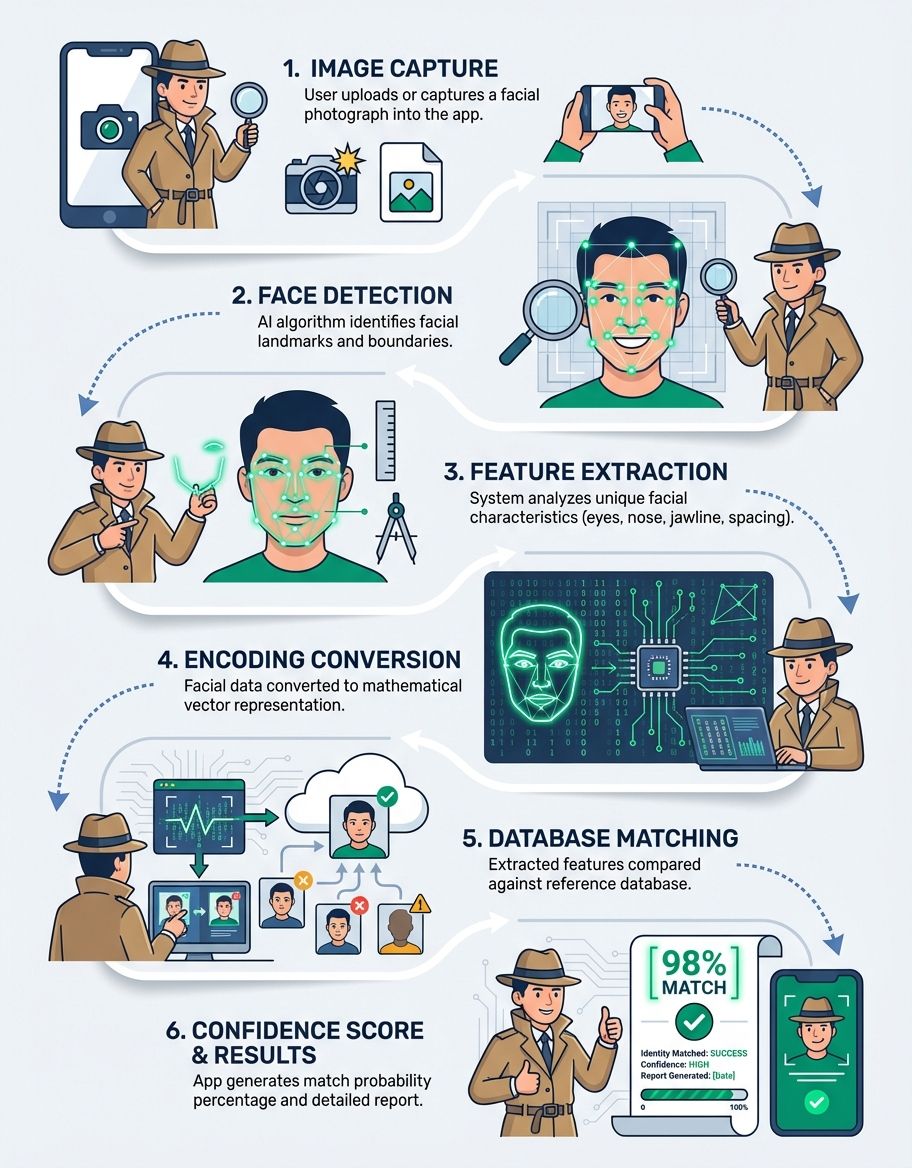
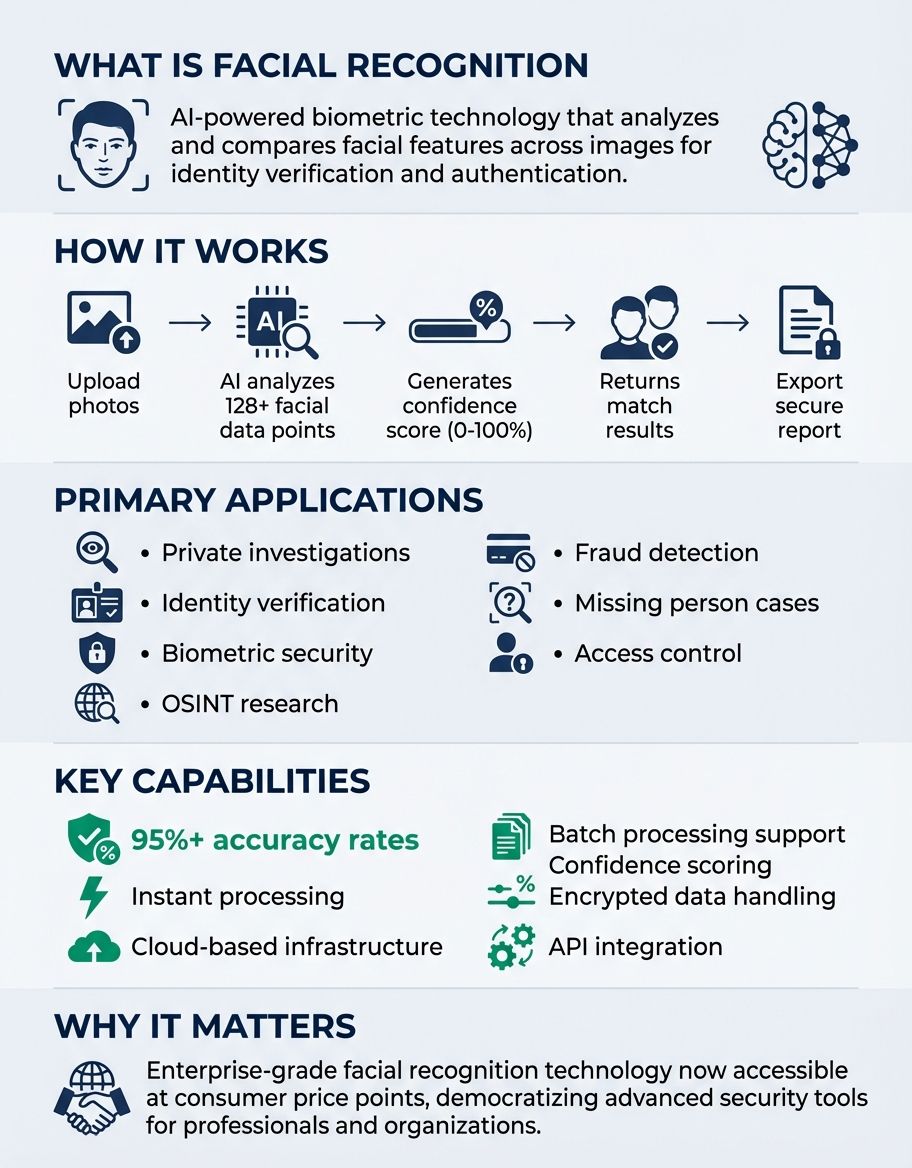
face matching technology works by analyzing unique face characteristics to create a mathematical representation of a person's face. The best biometric authentication app solutions use advanced algorithms that map key face landmarks, measuring distances between eyes, nose, mouth, and other distinctive features. This biometric information creates a unique biometric signature that enables rapid identification and verification.
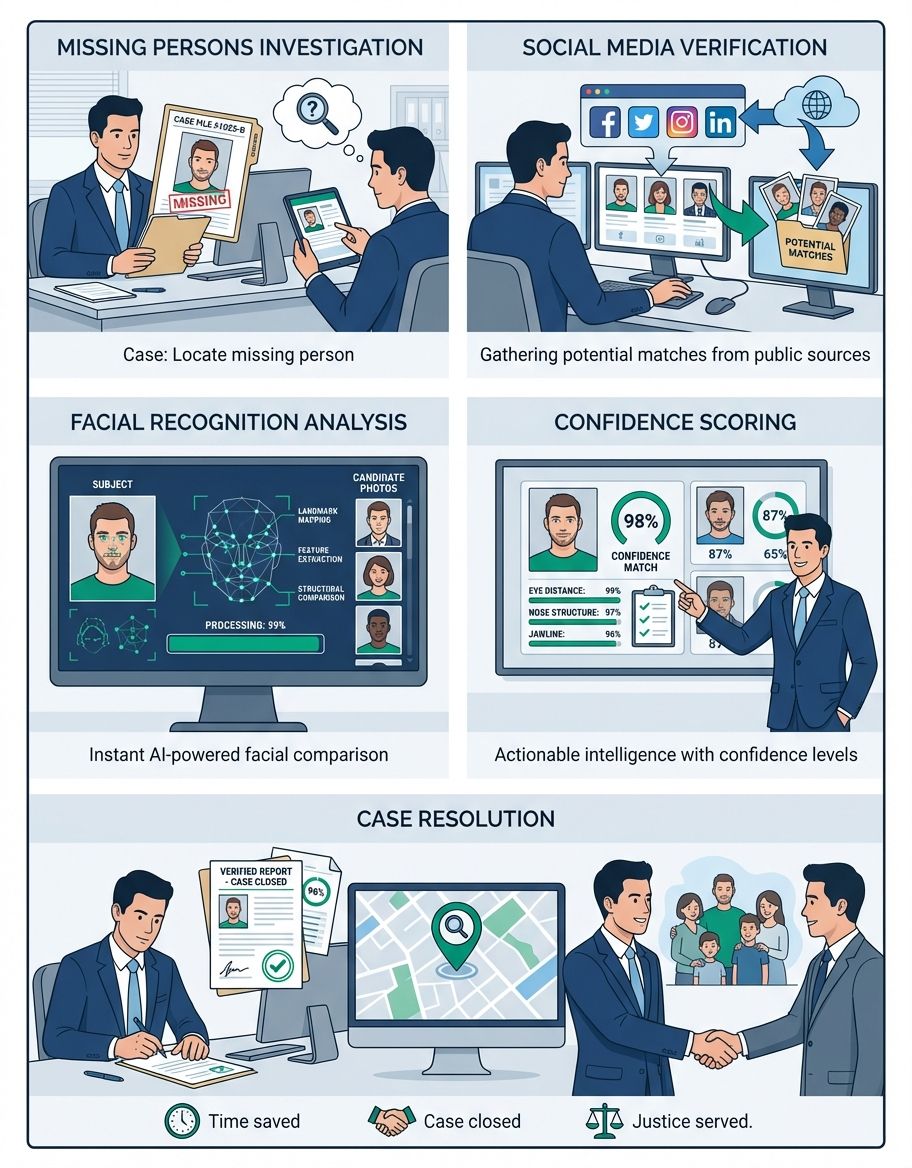
Modern face identification systems process images through multiple stages. First, the app detects faces within an image using specialized algorithms. Next, it aligns the face characteristics to standardize positioning. The system then extracts distinctive features and converts them into numerical data that can be compared against stored templates. This process happens in milliseconds, making identity verification both convenient and efficient for users.
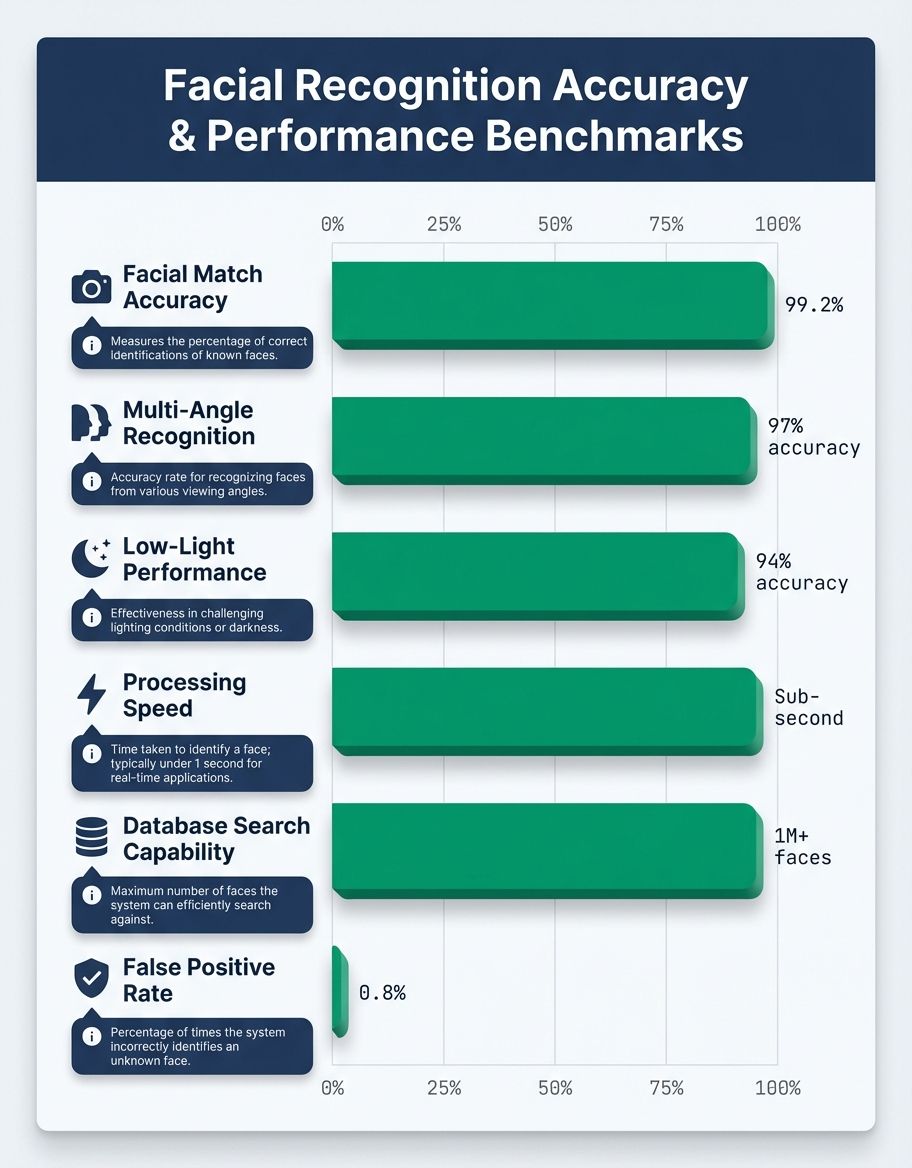
The accuracy of face matching depends on several factors including image quality, lighting conditions, and the sophistication of the underlying algorithms. Leading apps continuously improve their face detection capabilities through machine learning, training their systems on diverse datasets to recognize faces across various ethnicities, ages, and environmental conditions. This ensures reliable performance regardless of user demographics or picture quality.
Privacy-conscious users should understand that face information represents sensitive biometric information. Reputable facial identification platforms implement robust protective measures to safeguard this data from unauthorized access. Encryption, secure storage protocols, and transparent information handling policies distinguish quality apps from less trustworthy alternatives in the competitive facial recognition market.
Essential protection capabilities in face matching apps
Security stands as the cornerstone of any reliable biometric authentication app. The best services implement multiple layers of protection to safeguard user data and prevent unauthorized access. End-to-end encryption ensures that face information remains secure during transmission and storage, making it virtually impossible for malicious actors to intercept or misuse biometric information.
Advanced protection capabilities include liveness detection, which prevents spoofing attempts using photos or videos. These mechanisms verify that a real person is present during authentication rather than a static image. Multi-factor authentication combines facial recognition with additional verification methods, creating robust protection that protects against various attack vectors.
Leading facial recognition apps also implement secure information storage practices. Rather than storing actual face photos, many services convert faces into encrypted mathematical templates that cannot be reverse-engineered to recreate the original picture. This approach protects user privacy while maintaining the functionality of the recognition system.
Regular security audits and compliance with international information protection standards demonstrate a provider's commitment to security. Apps that undergo independent security reviews and maintain certifications like ISO 27001 offer greater assurance of their defense posture. Users should prioritize services that transparently communicate their security practices and regularly update their systems to address emerging threats.
Comprehensive Review of Leading Facial identification platforms
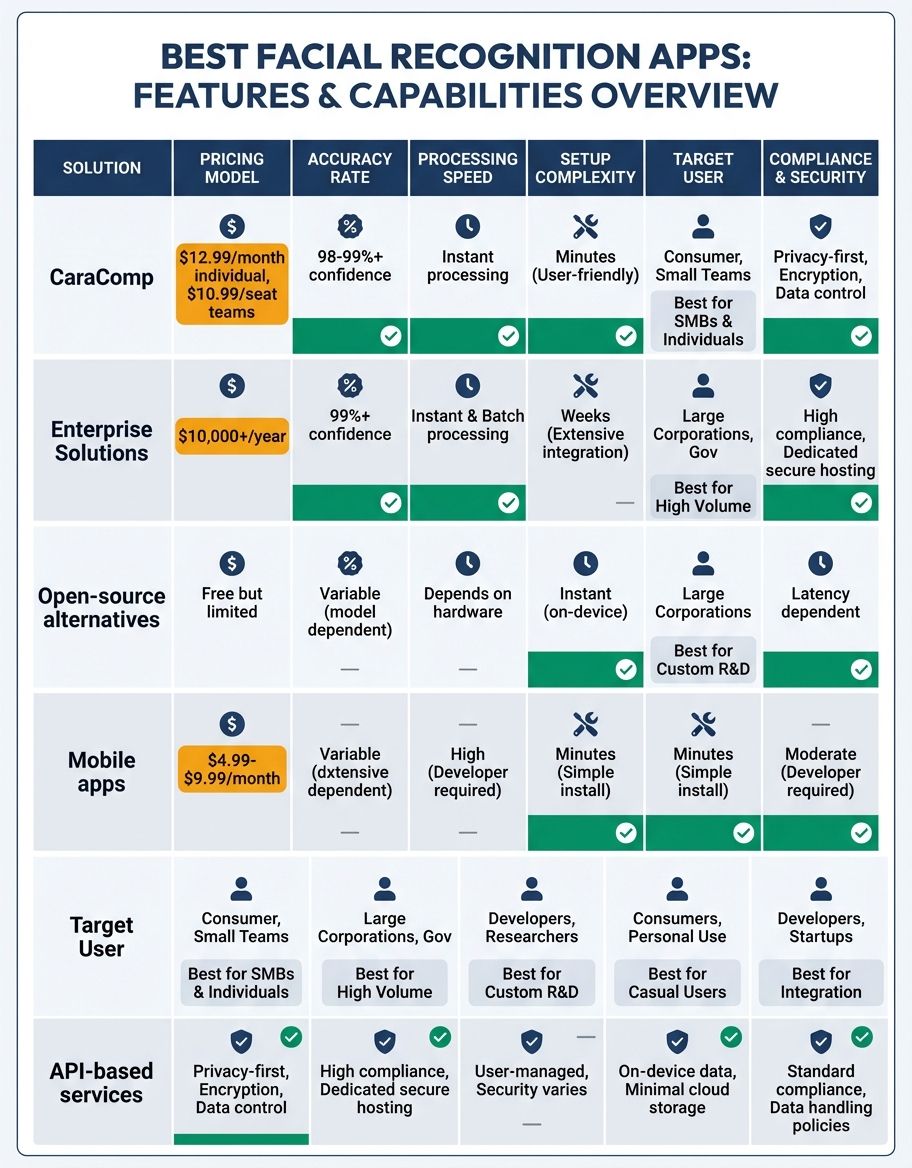
the biometric recognition market offers numerous services, each with distinct strengths and capabilities. Understanding the features and limitations of popular options helps users identify the best biometric authentication app for their specific needs. This review examines key players in the space, evaluating their performance, security, and user experience.
Consumer-focused apps like FaceApp have popularized facial identification technology for entertainment purposes, but professional-grade services like Clearview AI serve law enforcement and security organizations. PimEyes offers public facial search capabilities, allowing users to find images of themselves across the internet. Each service targets different use cases with varying levels of accuracy and privacy protection.
Enterprise solutions provide more robust features for organizational needs. these solutions often include API access, batch processing capabilities, and integration with existing protection infrastructure. Mobile Fortify and similar platforms focus on mobile device protection, using biometric scanning to safeguard access to sensitive apps and data on smartphones and tablets.
When conducting a thorough review of services, consider factors beyond basic biometric matching accuracy. Look for responsive customer support, regular feature updates, transparent pricing models, and clear privacy policies. The best providers balance powerful capabilities with responsible data handling and user control over personal information.
photo lookup and Recognition Capabilities
photo lookup functionality extends facial recognition beyond simple verification, enabling users to find pictures of specific individuals across vast photo collections. This capability has applications ranging from organizing personal photo libraries to locating images across public databases. Advanced photo lookup algorithms can identify faces even when partially obscured or photographed from unusual angles.
The technology behind facial photo lookup combines traditional computer vision with modern deep learning approaches. Neural networks trained on millions of images learn to recognize subtle face characteristics that distinguish individuals. These systems can process thousands of photos per second, making large-scale photo lookup practical for both consumer and professional applications.
Privacy considerations around picture search have sparked important conversations about consent and information usage. While some services freely index publicly available photos, others require explicit permission before including someone in their searchable database. Users should understand how different platforms handle image data and what control they offer over personal pictures appearing in search results.
Practical applications of facial picture search include finding photos from events, identifying unknown individuals in family photo archives, and monitoring online presence. For personal users, these capabilities provide convenient ways to organize and rediscover memories. Businesses leverage picture search for customer recognition, security monitoring, and marketing analytics.
Data Privacy and Protection in Facial Recognition
Data privacy represents a critical concern when using biometric scanning technology. biometric information carries unique risks because, unlike passwords, you cannot change your face if your information is compromised. Understanding how apps collect, store, and use face information helps users make informed decisions about which services to trust with their biometric information.
Leading facial recognition apps implement strict data minimization principles, collecting only the information necessary for their stated purposes. They provide clear privacy policies explaining what data they gather, how long they retain it, and who may access it. Transparency about information practices builds user trust and demonstrates commitment to responsible information stewardship.
Regulatory frameworks like GDPR in Europe and CCPA in California establish important protections for biometric information. Compliant services offer users rights including data access, correction, and deletion. Users can request information about what face information an app has stored and demand its removal. These protections ensure individuals maintain control over their personal biometric information.
Secure data handling extends beyond storage to encompass information sharing and third-party access. Reputable services limit data sharing to essential partners and never sell biometric information to advertisers or data brokers. When sharing is necessary for service functionality, users should receive clear notice and retain the right to opt out without losing core features.
Organizations deploying facial recognition must balance protection benefits against privacy implications. Best practices include obtaining informed consent, implementing purpose limitations, and conducting privacy impact assessments. These measures ensure biometric deployment respects individual rights while delivering intended security or convenience benefits.
core capabilities That Define Quality Recognition Apps
Identifying quality facial recognition apps requires evaluating several essential capabilities beyond basic face matching. Speed and accuracy form the foundation, but truly excellent apps offer additional capabilities that enhance user experience and expand functionality. Real-time processing enables instant verification, crucial for applications like access control where delays frustrate users.
Compatibility across devices and platforms extends an app's utility. Services that work seamlessly on iOS, Android, and web browsers provide flexibility for users with diverse technology ecosystems. cloud capabilities enable synchronization across devices, ensuring consistent access to facial recognition capabilities regardless of which device you're using.
Customization options allow users to tailor recognition sensitivity and security levels to their specific needs. Some situations demand maximum protection even if it occasionally requires additional verification steps. Others prioritize convenience, accepting slightly higher false acceptance rates for smoother user experiences. The best apps provide granular control over these trade-offs.
Integration capabilities determine how well a biometric recognition app works within existing workflows. APIs and SDKs allow programmers to incorporate identification capabilities into custom applications. Support for common authentication protocols ensures compatibility with enterprise identity management systems. These technical features expand an app's applicability beyond standalone use cases.
User interface design significantly impacts the practical utility of face matching apps. Intuitive controls, clear feedback during recognition attempts, and helpful error messages create positive experiences. Well-designed apps guide users through setup, optimize camera positioning, and explain security features without overwhelming less technical users.
Comparing Popular Facial Recognition Applications
Comparing facial recognition apps reveals significant differences in capabilities, pricing, and intended use cases. This comprehensive review helps users identify which service best matches their requirements, whether seeking personal security features or professional-grade recognition capabilities.
| Application | Primary Use Case | Security Level | Platform Support | Notable Features |
|---|---|---|---|---|
| Face ID | Device Authentication | Very High | iOS, iPadOS | Hardware-integrated secure enclave, liveness detection |
| Windows Hello | Device & Account Access | High | Windows 10+ | Microsoft account integration, enterprise features |
| PimEyes | Public picture search | Medium | Web | Internet-wide facial search, privacy monitoring |
| Clearview AI | Law Enforcement | Very High | Web, Mobile | Massive database, investigative tools |
| FaceApp | Photo Editing | Low | iOS, Android | AI-powered photo transformations, filters |
| Amazon Rekognition | Developer API | High | Cloud API | Scalable, emotion detection, age estimation |
| Microsoft Azure Face | Enterprise Solutions | Very High | Cloud API | Enterprise compliance, advanced analytics |
Each application serves distinct needs with varying strengths. Device-integrated solutions like Face ID offer seamless security for everyday authentication. cloud platforms provide scalability for organizations processing large volumes of facial verification requests. Specialized tools target specific use cases from photo editing to investigative work.
Pricing models vary significantly across facial recognition services. Consumer apps often use freemium models with basic features available free and advanced capabilities requiring subscriptions. Enterprise solutions typically charge based on usage volume, measured in API calls or faces processed. Understanding pricing structures helps organizations budget appropriately for their facial recognition needs.
Implementation Best Practices for Facial Recognition
Successfully implementing facial recognition requires following established best practices that ensure security, accuracy, and user acceptance. Organizations deploying these systems must address technical, legal, and ethical considerations to maximize benefits while minimizing risks and securing user privacy.
Begin implementation with clear objectives and success criteria. Define specific use cases where facial recognition adds genuine value rather than deploying the technology simply because it's available. Whether enhancing physical security, streamlining authentication, or improving customer experience, well-defined goals guide appropriate technology selection and deployment strategies.
Conduct thorough testing before full deployment to ensure system accuracy across diverse user populations. Facial matching algorithms can exhibit varying performance across different demographics if not properly trained. Testing with representative user groups identifies potential biases or accuracy issues that require correction before the system goes live.
Provide clear communication to users about how facial recognition works, what data is collected, and how it's protected. Transparency builds trust and increases user acceptance. Offer alternative authentication methods for users uncomfortable with facial recognition, ensuring inclusive access regardless of personal technology preferences or concerns.
Establish robust data governance frameworks covering the entire lifecycle of facial data from collection through eventual deletion. Define retention periods, access controls, and deletion procedures. Regular audits verify compliance with established policies and identify opportunities for strengthening privacy protections.
Monitor system performance continuously, tracking accuracy metrics and user feedback. Facial identification technology evolves rapidly, and regular updates ensure systems maintain optimal performance and security. Stay informed about emerging threats and adjust protective measures proactively to protect against new attack vectors.
Frequently Asked Questions
How does verifying people's identities using their faces work?
Verifying people's identities using their faces involves capturing a face photo, extracting unique biometric features like the distance between eyes and nose shape, and comparing these capabilities against previously stored templates. The system calculates a similarity score, and if it exceeds a predetermined threshold, the identity is verified. Modern systems use neural networks trained on millions of faces to achieve high accuracy even in challenging conditions.
What should I look for when reviewing facial recognition apps?
When conducting a review of facial recognition apps, evaluate security features, accuracy rates, privacy policies, and user experience. Examine how the app stores and protects facial data, whether it includes liveness detection to prevent spoofing, and what control you have over your biometric information. Consider the app's intended use case and whether its features align with your specific needs.
How does identifying work in face identification systems?
Identifying individuals through facial recognition involves comparing a captured face photo against a database of known faces to determine who the person is. Unlike verification which confirms a claimed identity, identification searches through potentially thousands or millions of stored faces to find matches. This process requires more computational power and typically takes longer than simple verification, but modern systems can search large databases in seconds.
How does Clearview AI work?
Clearview AI works by scraping billions of images from public websites and social media platforms, creating a massive searchable database of faces. Law enforcement and authorized organizations can upload a picture of an unknown person, and the system searches its database to find matching images along with their source URLs. This provides investigators with potential identity leads, though the service has sparked significant privacy debates about consent and surveillance.
How does PimEyes work?
PimEyes works by allowing users to upload a photo and search for similar faces across publicly available images on the internet. The service indexes photos from websites, blogs, and other online sources, enabling users to find where their face appears online. While marketed as a privacy tool to help people monitor their online presence, it also raises concerns about enabling unauthorized tracking of individuals.
How does Mobile Fortify work?
Mobile Fortify works by adding an extra layer of security to mobile devices through facial recognition authentication. The app secures access to individual applications, requiring facial verification before sensitive apps open. It provides detailed access logs, sends alerts for failed authentication attempts, and allows users to customize protection settings for different apps based on their sensitivity levels.
How does FaceApp work?
FaceApp works using artificial intelligence to modify face characteristics in photos, applying filters that age, rejuvenate, or otherwise transform appearances. While it uses facial recognition to identify and map face characteristics, its primary purpose is entertainment rather than security or identification. The app analyzes face structure and applies realistic transformations using neural networks trained on countless face photos.
Conclusion: Selecting Your Ideal biometric solution
Choosing the best biometric authentication app depends on your specific requirements, whether prioritizing security, convenience, privacy, or specialized capabilities. Consumer users seeking device protection benefit from integrated solutions like Face ID that offer seamless, secure authentication. Organizations requiring scalable recognition capabilities should evaluate enterprise solutions with robust APIs and compliance certifications.
As facial identification technology continues advancing, new capabilities and capabilities regularly emerge. Stay informed about developments in accuracy, security, and privacy protection. Regularly review your chosen app's performance and reassess whether it continues meeting your needs or if newer alternatives offer superior capabilities.
The future of facial recognition promises enhanced accuracy, stronger security features, and better privacy protections. Emerging technologies like federated learning enable powerful facial recognition while keeping personal information on individual devices. These innovations will expand the applications of facial recognition while addressing current privacy concerns.
Whether you're an individual protecting personal devices or an organization implementing large-scale facial identification systems, carefully evaluate the features, security measures, and information practices of available services. The best biometric authentication app for your needs balances powerful capabilities with responsible data handling and user-friendly design. By understanding the key factors discussed in this guide, you can confidently select a solution that delivers the authentication and functionality you require while respecting privacy and maintaining ethical standards.
